腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Android ] For an unspecified reason, Google switched all the Nexus factory image files to ZIP (instead of TGZ) today. http://droidsec.org/nexus updated!
" 不知道什么原因, Google 将出厂时的 Nexus 镜像文件切换至 ZIP 格式,不再采用 TGZ: https://t.co/HLnhoN3CiX "
-

[ Android ] How Trojans manipulate Google Play https://securelist.com/blog/research/75894/how-trojans-manipulate-google-play/
"Android 木马是如何调戏 Google Play 的: https://t.co/p91Q4JBUfP"
-

[ Attack ] Dropbox Data Breach, more than 68 Million account details leaked online http://securityaffairs.co/wordpress/50803/data-breach/dropbox-data-breach.html
"Dropbox 6800 万账户信息泄漏,该事件发生于 2012 年: https://t.co/qIZN6goyDK"
-

[ Browser ] Stealing all browser data (passwords,history etc.) from Yandex Browser by exploiting a CSRF in Yandex's sync system https://www.netsparker.com/blog/web-security/csrf-vulnerability-yandex-browser/
" Yandex 浏览器的一个 CSRF 漏洞: https://t.co/DRiD5ZKZzJ "
-

[ Crypto ] New cloud attack takes full control of virtual machines with little effort http://arstechnica.com/security/2016/08/new-attack-steals-private-crypto-keys-by-corrupting-data-in-computer-memory/ by @ dangoodin001
" 针对云的攻击 - 在 RowHammer 的面前,现有的加密软件显得脆弱无力: https://t.co/bPVZh39Iht "
-

[ Detect ] Best paper I've ever read for Intrusion detection with Windows Events! https://cyber-ir.com/2016/08/27/intrusion-detection-with-windows-event-ids/ #dfir #ThreatHunting
" 基于 Windows 事件日志的入侵检测: https://t.co/P9beVnc0HU "
-

[ Fuzzing ] NCC Group Open Source: Hodor Fuzzer - a generic fuzzer design - https://github.com/nccgroup/hodor by Joel St. John, Braden Hollembaek, and Frank Arana
" Hodor - 通用型 Fuzzer,NCC Group 开源的: https://t.co/DPukdKHP0s"
-

[ IoTDevice ] Exploiting PS Vita kernel: sceNetIoctl use-after-free https://blog.xyz.is/2016/vita-netps-ioctl.html
"利用 SceNetPs 模块的一个 UAF 漏洞攻击 PS Vita 内核: https://t.co/AzEoVfzgI1"
-

[ Linux ] So I lost my OpenBSD FDE password - reversing the metadata and building a bruteforcer https://blog.filippo.io/so-i-lost-my-openbsd-fde-password/
" 我忘了我的 OpenBSD 全盘加密(FDE)的密码: https://t.co/7ZuyqYcn6p"
-

[ MachineLearning ] Baidu releases deep learning framework - nice work @ AndrewYNg https://twitter.com/jeremyphoward/status/770760275213430784
"百度开源了自己的深度学习平台 PaddlePaddle: https://github.com/baidu/paddle "
-

[ Operating System ] #Genode 16.08 released https://genode.org/documentation/release-notes/16.08
" Genode 操作系统框架发布 16.08 版本: https://t.co/Tl2o7k8sh7"
-

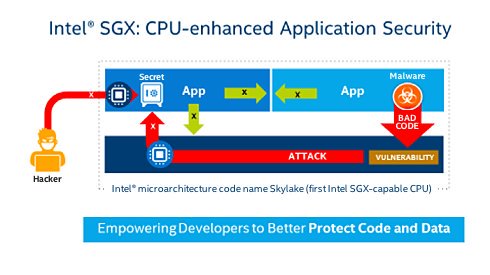
[ Others ] Using #Intel #SGX to Protect On-line #Credentials. Read this http://ow.ly/pyQ4303DcZi https://t.co/3fpB29uXDy
" 用 Intel SGX 保护在线凭据信息: https://t.co/IpJzgsrIq1 "
-

[ Others ] Comma Separated Vulnerabilities explanation (With different attack vectors) - http://www.contextis.com/resources/blog/comma-separated-vulnerabilities/
" 逗号分隔的漏洞,公式注入漏洞,来自 Context Blog: https://t.co/Yeai410V7r"
-

[ Others ] New #infosec course by the Dr. himself @ JaredDeMott "Sec for #hackers & #devs: Code Auditing" @ pluralsight https://app.pluralsight.com/library/courses/code-auditing-security-hackers-developers/table-of-contents
" 面向黑客和开发者的代码审计视频教程: https://t.co/Yn05v7t0Qc"
-

[ Others ] Smaller and faster data compression with Zstandard https://code.facebook.com/posts/1658392934479273/smaller-and-faster-data-compression-with-zstandard/
" Facebook 公开的新压缩算法 Zstandard,更快,压缩比更高: https://t.co/WKXTlXRuWk"
-

[ Others ] Code Injection and Its Types- Part 1 http://resources.infosecinstitute.com/code-injection-types-part-1/
"代码注入及其类型 Part 1,来自 InfoSec Blog: https://t.co/7jcznrBPmG"
-

[ Others ] Fake ransomware spreading via Redis compromise: https://duo.com/blog/over-18-000-redis-instances-targeted-by-fake-ransomware
" Redis 服务器设计是运行在可信环境的,Duo 团队发现,超过 18000 台 Redis 服务器暴露在互联网。勒索软件早就盯上了︰ https://t.co/vk0p0ZvFLw"
-

[ Protocol ] Attacking SS7: Mobile Operators Security Analysis http://blog.ptsecurity.com/2016/08/attacking-ss7-mobile-operators-security.html
" Attacking SS7,手机运营商安全性分析: https://t.co/js4zipozm2"
-

[ Tools ] New version of Sysinternals Suite is out https://technet.microsoft.com/en-us/sysinternals/bb842062
"Sysinternals 工具套件更新新版本: https://t.co/Rkeqv2wWXU"
-

[ Tools ] SQL Map tamper scripts guide - http://www.forkbombers.com/2016/07/sqlmap-tamper-scripts-update.html
"SQL Map 篡改脚本指南: https://t.co/BasouuGQyd"
-

[ Windows ] Windows 10 symbols are on symbol server finally. Yay! It turns out the best email address for symbol bugs is on: https://developer.microsoft.com/en-us/windows/hardware/download-symbols
"Windows 的调试符号下载︰ https://t.co/SIyzjXBxtU 包括 Windows 10 的符号 "