腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Android ] Another Qualcomm kernel buffer overflow not included in the August security update: https://www.codeaurora.org/buffer-overflow-vulnerability-wcnsswlanwrite-cve-2016-5342. Including this for 5X/6P too.
" 高通的内核缓冲区溢出漏洞(CVE-2016-5342)︰ https://www.codeaurora.org/buffer-overflow-vulnerability-wcnsswlanwrite-cve-2016-5342 "
-

[ Attack ] German speakers targeted by Ozone RAT campaign #fortiguard https://blog.fortinet.com/2016/08/29/german-speakers-targeted-by-spam-leading-to-ozone-rat
" 德语用户遭到了 Ozone 远控的攻击,来自 Fortinet Blog: https://t.co/aTsHSXjxqn"
-

[ Attack ] 71,000 Minecraft World Map accounts leaked online after 'hack' http://www.theregister.co.uk/2016/08/30/71000_minecraft_world_map_accounts_leak/
"71000 Minecraft World Map 游戏账户泄漏: https://t.co/yurdZLGING"
-

[ Attack ] Exploring the Cybercrime Underground: Part 2 – The Forum Ecosystem http://researchcenter.paloaltonetworks.com/2016/08/unit42-exploring-the-cybercrime-underground-part-2-the-forum-ecosystem/
"探索网络犯罪(二)之论坛生态系统,来自 Palo Alto: https://t.co/U0GDYGPStF"
-

[ Attack ] Kuwait Automotive Imports Company Hacked; 10k Accounts Leaked https://www.hackread.com/kuwait-automotive-imports-company-hacked/
"科威特汽车进口公司被黑,10000 账户信息泄漏: https://t.co/Cexs1LO7DM"
-

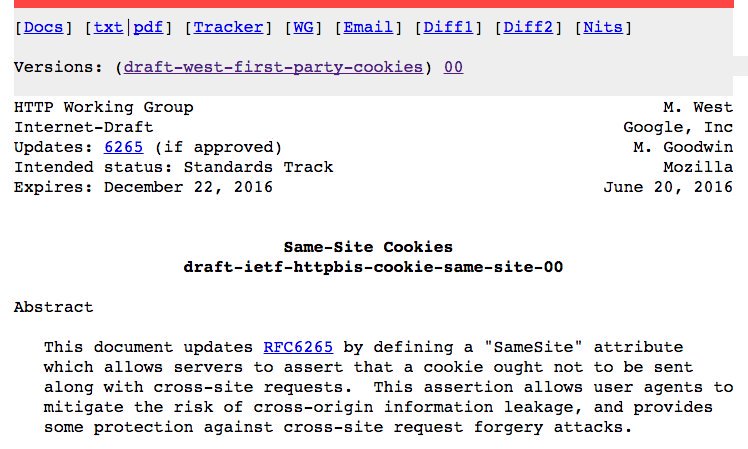
[ Browser ] Stop Cross-Site Timing Attacks with SameSite cookies: http://bit.ly/2bDDJ8C... and cross-site forgery in general. https://t.co/VkqbSUMTkg
" 利用 SameSite 特性阻断跨站时序攻击: https://www.igvita.com/2016/08/26/stop-cross-site-timing-attacks-with-samesite-cookies/ "
-

[ Crypto ] Argon2 compiled for browsers with asm.js and WebAssembly https://github.com/antelle/argon2-browser
" Argon2,密码哈希竞赛 (PHC) 的获奖算法,该库的的浏览器运行时库版本: https://t.co/egrYUiIUgg"
-

[ Crypto ] PyQemu - dynamic binary instrumentation based crypto detection framework. https://github.com/pleed/pyqemu
"PyQemu - 基于动态二进制插桩的加密检测框架: https://t.co/gRS9NYHdNt 相关的论文: http://ieeexplore.ieee.org/application/enterprise/entfilecabinetfull.jsp?ResultStart=0&arnumber=6461007 "
-

[ Fuzzing ] NCC Group Research Insights Volume 9 - Modern Security Vulnerability Discovery - is out! - https://www.nccgroup.trust/uk/our-research/research-insights-vol-9-modern-security-vulnerability-discovery/?research=Whitepapers https://t.co/0K9IbWLGHo
-

[ macOS ] OSX/Keydnap spreads via signed Transmission application http://www.welivesecurity.com/2016/08/30/osxkeydnap-spreads-via-signed-transmission-application/ via @ ESET
"OSX/Keydnap 恶意软件通过有签名的 Transmission APP 捆绑传播: https://t.co/dTedY4JkQW "
-

[ Malware ] Malware Analysis – Dridex Loader – Part 2 https://countuponsecurity.com/2016/08/28/malware-analysis-dridex-loader-part-2/
" Dridex 勒索软件的加载器分析: https://t.co/f4rlEYD7sy"
-

[ Malware ] Inside the Demise of the Angler Exploit Kit https://threatpost.com/inside-the-demise-of-the-angler-exploit-kit/120222/
" Angler Exploit Kit 的消亡过程,来自 ThreatPost 的报道: https://t.co/OFZjmhyHHa 来自卡巴斯基的报告《猎捕 Lurk 犯罪组织》: https://securelist.com/analysis/publications/75944/the-hunt-for-lurk/ "
-

[ Malware ] Double-click me not: Malicious proxy settings in OLE Embedded Script https://blogs.technet.microsoft.com/mmpc/2016/08/29/double-click-me-not-malicious-proxy-settings-in-ole-embedded-script/
" 随着 Windows 各项利用缓解措施的增强,攻击者更倾向于采用社会工程的方法诱导用户点击 OLE 对象脚本,以实现第一步攻击: https://t.co/rmcw2NRVn3 "
-

[ MalwareAnalysis ] Pythons and Unicorns and #Hancitor…Oh my! Decoding binaries through emulation http://bit.ly/2bYiuPA #Unit42
" 基于 Unicorn 引擎,调用恶意软件自身的解密代码,解密其 Payload: https://t.co/FK9UMJ2pE5 "
-

[ Others ] The slides from my @ BSidesMCR talk "Hunting Asynchronous Vulnerabilities" are available at https://portswigger.net/knowledgebase/papers/HuntingAsynchronousVulnerabilities2.pdf Video coming soon!
" 挖掘异步类问题相关的漏洞: https://t.co/ls4WCk1JQq "
-

[ Others ] Mobile Security News Update August 2016 https://www.mulliner.org/blog/blosxom.cgi/security/mobile_security_news_update_august2016.html Much Mobile Malware (also more regular updates from now on!)
" Collin R. Mulliner 总结的 8 月份的移动安全动态: https://t.co/AzqbDN5x32 "
-

[ Others ] How to Leak Data From Air-Gapped Computers With a USB Device: https://threatpost.com/how-to-leak-data-from-air-gapped-computers-with-a-usb-device/120221/ via @ threatpost
" 在物理隔离的计算机间通过 USB 偷数据,来自 ThreatPost: https://t.co/2MF9rbFGRr"
-

[ Rootkit ] The SMM Rootkit Revisited: Fun with USB (paper published at ARES 2014): https://www.computer.org/csdl/proceedings/ares/2014/4223/00/4223a279.pdf
-

[ Tools ] HanzoInjection injecting arbitrary codes in memory to bypass common antivirus solutions https://github.com/P0cL4bs/hanzoInjection
"HanzoInjection - 向内存中注入代码并且可以躲避常见杀软的工具: https://t.co/Pqvxv8sFfL"
-

[ Virtualization ] PV Calls: a new paravirtualized protocol for POSIX syscalls - https://blog.xenproject.org/2016/08/30/pv-calls-a-new-paravirtualized-protocol-for-posix-syscalls/
"PV Calls - 从 DOMU 到 DOM0 转发 Syscall 的协议: https://t.co/EsvRaDzPhR"
-

[ Web Security ] The Easiest Way to Bypass XSS Mitigations http://brutelogic.com.br/blog/the-easiest-way-to-bypass-xss-mitigations/
" Bypass Sucuri 的 XSS 缓解防护: https://t.co/nIDK7thDrc"
-

[ Windows ] [Blog Post] http://subt0x10.blogspot.com/2016/08/advanced-use-case-for-sct-files.html Advanced Use Cases and Bypass with .SCT Files. regsvr32.exe/certutil.exe Feedback Welcome.
" .SCT 文件的高级用法: https://t.co/tjoiKBQbao "
-

[ Windows ] Doesn't carbonblack have a filter driver to catch SET_REPARSE_POINT FSCTL rather than check cmdline for mklink? https://www.carbonblack.com/2015/08/05/bit9-carbon-black-threat-research-team-unveils-nefarious-intents-of-volume-shadows-copies/
" 磁碟区卷影(Volume Shadows Copies)是如何工作的: https://t.co/9yLpr5kAsN"