腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Android ] ParseDroid - 来自 CheckPoint 的研究员提出了一个 Android 生态环境的攻击面 - 开发者工具,以 APKTool 为例,他们在 APKTool 的第三方 XML 库中找到了一个 XXE,下载使用 APKTool 的开发者/研究员就可能被攻击: https://threatpost.com/developers-targets-in-parsedroid-poc-attack/129088/ https://research.checkpoint.com/parsedroid-targeting-android-development-research-community/
-

[ Browser ] OOB access in v8 wasm after Symbol.toPrimitive overwrite,这是 Chrome 9 月份修复的由 Choongwoo Han 报告的 v8 漏洞(CVE-2017-5122): https://bugs.chromium.org/p/chromium/issues/detail?id=752423
-

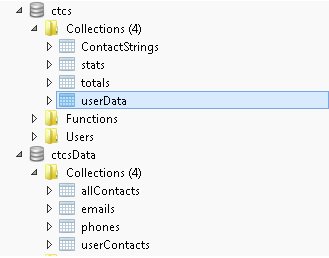
[ Industry News ] 个性化虚拟键盘开发者泄露了 3100 万个客户端注册文件: https://mackeepersecurity.com/post/virtual-keyboard-developer-leaked-31-million-of-client-records
-

[ Industry News ] 惠普和华硕发布第一款 Windows 10 ARM PC: http://arstechnica.com/gadgets/2017/12/hp-asus-announce-first-windows-10-arm-pcs-20-hour-battery-life-gigabit-lte/
-
-

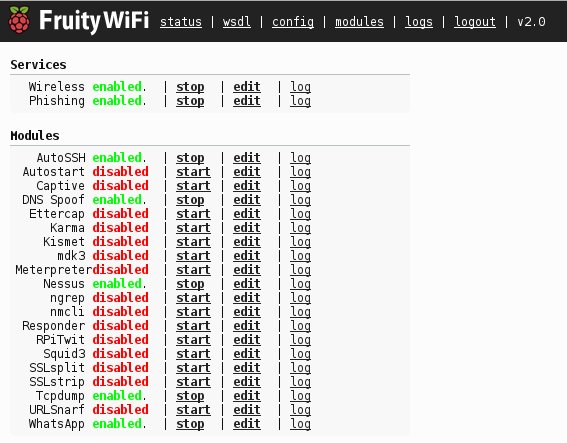
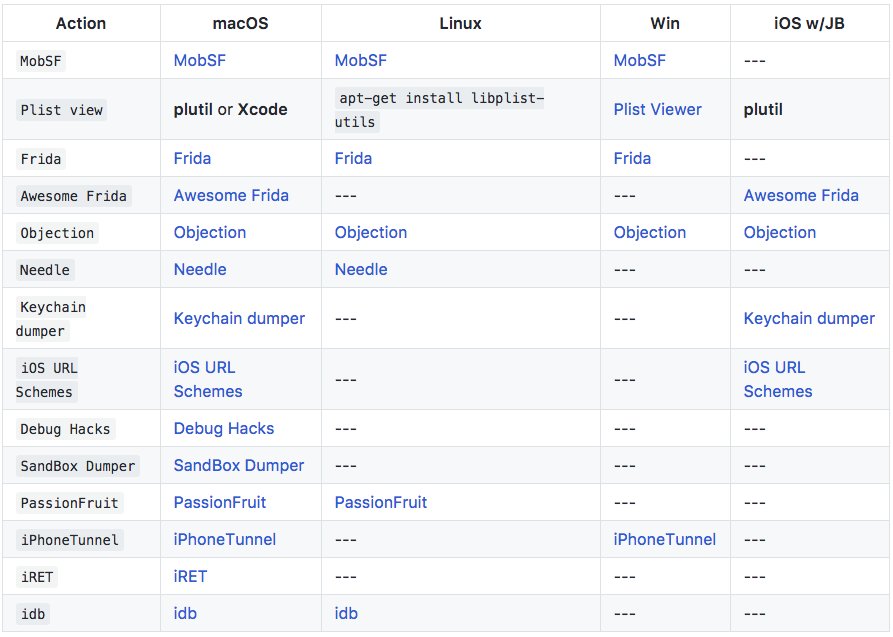
[ iOS ] iOS 设备上的恶意恶意软件: https://dsec.ru/upload/medialibrary/29f/29f57cef406125e9169da733e1aaf83f.pdf
-

[ iOS ] iOS 11.2 修复的 IOSurfaceRootUserClient Port UAF 漏洞的分析,来自盘古团队 Blog: http://blog.pangu.io/iosurfacerootuserclient-port-uaf/
-

[ Malware ] DRIDEX 回归,NECURS 僵尸网络通过垃圾邮件推送 DRIDEX: http://malware-traffic-analysis.net/2017/12/04/index2.html
-

[ Malware ] DoubleHidden 恶意软件隐藏在 Google Play 商店: https://www.symantec.com/blogs/threat-intelligence/doublehidden-android-malware-google-play
-

[ Others ] Forcepoint 对 Quant Loader 的分析报告: https://blogs.forcepoint.com/security-labs/quantize-or-capitalize?adbsc=forcepoint74932977&adbid=938089194953482241&adbpl=tw&adbpr=17244740
-

[ Others ] JavaScript Zero:缓解 JavaScript 0day 攻击的解决方案 : https://misc0110.net/web/files/jszero.pdf
-

[ Pentest ] 通过追踪事件日志发现横向渗透攻击(第2版): http://blog.jpcert.or.jp/2017/12/research-report-released-detecting-lateral-movement-through-tracking-event-logs-version-2.html
-

[ Popular Software ] TeamViewer_Permissions_Hook_V1 - 通过向 TeamViewer 注入 DLL 并改写内存的方式实现对特殊功能限制的破解,譬如特殊菜单的启用: https://github.com/gellin/TeamViewer_Permissions_Hook_V1TeamViewer 紧急推出了补丁,已修复这个问题: https://threatpost.com/teamviewer-rushes-fix-for-permissions-bug/129096/
-
-
-

[ Tools ] Mailsploit - 邮箱客户端的漏洞利用工具套件,集成了 30 款主流邮箱客户端(Apple Mail、Thunderbird、Yahoo! Mail、ProtonMail 等)的漏洞: https://www.mailsploit.com/index
-
-

[ Browser ] 继 Chromium 之后,Firefox 也开始支持 Headless 模式运行,方便浏览器的自动化控制: https://hacks.mozilla.org/2017/12/using-headless-mode-in-firefox/
-

[ Browser ] Edge 浏览器通过 Media Extensions 来实现扩充对未知媒体文件格式的支持: https://blogs.windows.com/msedgedev/2017/12/05/introducing-web-media-extension-package-ogg-vorbis-theora-support/#VVBJi1Cwwm3F4q4k.97
-

[ Browser ] 在 Firefox 中使用 Headless 模式: https://hacks.mozilla.org/2017/12/using-headless-mode-in-firefox/
-
-
-

[ Malware ] 安全威胁预警:Mirai变种Satori正在端口 37215 和 52879 上类似蠕虫式传播: http://blog.netlab.360.com/wa-a-new-mirai-variant-is-spreading-in-worm-style-on-port-37215-and-52869/
-
-

[ Pentest ] 有效的隐藏红队基础设施的方法: https://posts.specterops.io/designing-effective-covert-red-team-attack-infrastructure-767d4289af43
-

[ Popular Software ] 2017 年的几个经典的 WordPress 插件漏洞分析: https://blog.ripstech.com/2017/wordpress-plugin-vulnerabilities-static-analysis/
-
-
-

[ Virtualization ] Windows 8.1 加密内存空间 CI!g_pStore 的 Warbird 虚拟机保护机制逆向分析: https://github.com/airbus-seclab/warbirdvm
-

[ Windows ] CIA Vault7 RDB中的Windows后门利用方法分析: https://3gstudent.github.io/3gstudent.github.io/CIA-Vault7-RDB%E4%B8%AD%E7%9A%84Windows%E5%90%8E%E9%97%A8%E5%88%A9%E7%94%A8%E6%96%B9%E6%B3%95%E5%88%86%E6%9E%90/