腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Data Breach ] PayPal 子公司 TIO 泄漏了 160 万客户数据: https://thehackernews.com/2017/12/paypal-tio-data-breach.html
-

[ Malware ] Ursnif 木马采用新的代码注入技术: https://threatpost.com/ursnif-trojan-adopts-new-code-injection-technique/129072/
-

[ MalwareAnalysis ] 恶意软件渗透传播技术(基于文件、邮件、域控等等)研究,以及以欺骗为核心的检测框架: https://zh.scribd.com/document/366244507/Spreading-Techniques-and-Deception-based-Detection-Acalvio-Technical-White-Paper
-

[ Obfuscation ] LLVM混淆器剖析 Part 1: https://blog.rpis.ec/2017/12/dissection-llvm-obfuscator-p1.html
-

[ Others ] 线上服务器 Go Runtime 一个诡异 Bug 的调试过程: https://marcan.st/2017/12/debugging-an-evil-go-runtime-bug/
-

[ Pentest ] Writing .NET Executables for Pentesters Part 2: https://www.peew.pw/blog/2017/12/4/writing-net-executables-for-penteters-part-2
-

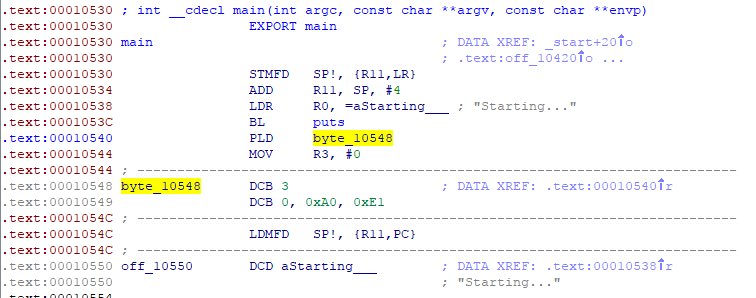
[ ReverseEngineering ] 对抗 IDA Pro 调试器 ARM 反汇编的技巧: https://kbdsmoke.me/anti-disassembly-on-arm-ida-specifically/
-

[ SCADA ] Automation Direct 公司的工控产品多个漏洞披露(CVE-2017-14020): https://www.mogozobo.com/?p=3432
-

[ SecurityAdvisory ] Android 12月安全公告发布: https://source.android.com/security/bulletin/2017-12-01 Pixel / Nexus 12月安全公告: https://source.android.com/security/bulletin/pixel/2017-12-01
-

[ SecurityReport ] Palo Alto Networks 发布 2018年安全网络安全预测 : https://researchcenter.paloaltonetworks.com/2017/12/2018-predictions-recommendations-cloud-security-adoption-will-disrupt-automotive-industry/
-

[ Tools ] HUNT - Burp Suite PRO 和 ZAProxy 的漏洞扫描插件: https://github.com/bugcrowd/hunt
-

[ Tools ] Microsoft Edge DevTools 开发者工具支持为 DOM 节点的变动设置调试断点了,可以设置三种断点(Subtree 变化、Node 删除、属性变化): https://blogs.windows.com/msedgedev/2017/12/04/dom-mutation-breakpoints-edge-devtools/#K5d1JyRCI0IfZ8YB.97
-
-

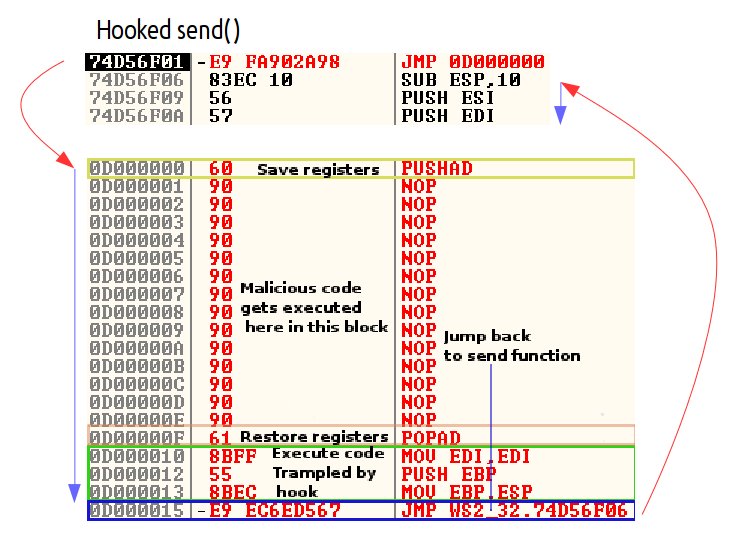
[ Windows ] 通过在函数 Prologue 部分检测 0xE9 (opcode JMP) 实现对 Inline Hook 的检测: https://userpc.net/2017/12/03/understanding-detecting-inline-hooks-winapi-hooks-ring3/
-

[ Windows ] Windows Defender ATP 利用机器学习和 AMSI 接口对抗基于脚本的攻击: https://blogs.technet.microsoft.com/mmpc/2017/12/04/windows-defender-atp-machine-learning-and-amsi-unearthing-script-based-attacks-that-live-off-the-land/?platform=hootsuite
-

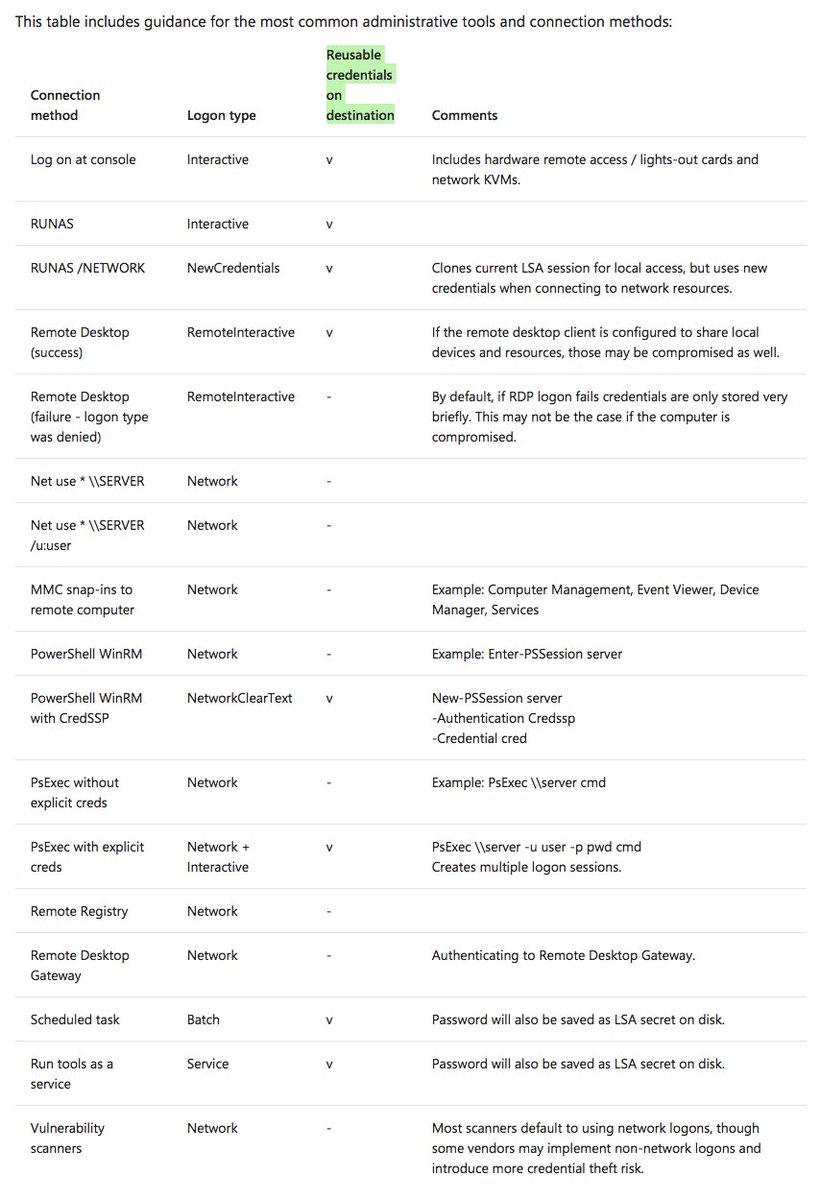
[ Windows ] 微软关于 Windows 特权访问防护的手册,其中介绍了不同的登陆类型(console、RUNAS、Remote Desktop、Net use * \SERVER 等等)及其限制: https://docs.microsoft.com/en-us/windows-server/identity/securing-privileged-access/securing-privileged-access-reference-material#ATLT_BM
-

[ Browser ] Firefox 57(Quantum)将启用新的主题 API: https://hacks.mozilla.org/2017/12/using-the-new-theming-api-in-firefox/
-
-

[ Conference ] hardwear.io 2017 会议的一篇演讲视频 - Shaking trust in hardware: https://www.youtube.com/watch?v=CWXL3tX00aU https://www.youtube.com/channel/UChwYb9xc9tZXquQxu4G0l_g/videos
-

[ Industry News ] Android 上的 Keybase 应用存在 bug,可能致使用户的私钥自动备份到 google 的服务器上: https://www.bleepingcomputer.com/news/security/keybase-bug-might-have-backed-up-your-private-encryption-key-on-googles-servers/
-

[ IoTDevice ] 小米IoT安全峰会-陈洋《小米IoT安全之路》: https://weibo.com/ttarticle/p/show?id=2309404181335387304911&display=0&retcode=6102
-

[ Linux ] 对Linux Kernel 4.14.0的SLAB_FREELIST_HARDENED加固实现的部分分析: https://hardenedlinux.github.io/system-security/2017/12/02/linux_kernel_4.14%E7%9A%84SLAB_FREELIST_HARDENED%E7%9A%84%E7%AE%80%E8%A6%81%E5%88%86%E6%9E%90.html?nsukey=D3MRM%2BIaOSiup9lNI9JP8vslv3UWopP%2FkD%2BvrANn5a49VgnvYhVMPCMv6sBTsi1cTxQCLjcIcd2GvrqZISJxA3LINp%2Bhlh%2FD2sG6l3iWqFRcDdcN70P6EGDL7bbaenz77CaiCKoTyjXrZPkTkTjnEga70OfZ4YO%2BESIvEfC33PfcRTcnPOdRLOnz8stw6HW4Z5OXsPUmAnDV3aEEIkxFJw%3D%3D&from=timeline&isappinstalled=0
-

[ MalwareAnalysis ] 针对 Emotet 银行木马的分析: https://blogs.technet.microsoft.com/mmpc/2017/12/04/microsoft-teams-up-with-law-enforcement-and-other-partners-to-disrupt-gamarue-andromeda/
-

[ Others ] Positive Technologies 团队在 GitHub 开源的几个项目介绍: http://blog.ptsecurity.com/2017/12/positive-technologies-on-github.html
-
-

[ ReverseEngineering ] 逆向工程师一直受到汇编垃圾代码(Junk Code)的折磨,FireEye 这篇 Blog 介绍如何识别 Junk Code: https://www.fireeye.com/blog/threat-research/2017/12/recognizing-and-avoiding-disassembled-junk.html
-

[ Tools ] 利用 Google 的 nsjail 工具为 ImageMagick 提供一个沙箱环境: https://offbyinfinity.com/2017/12/sandboxing-imagemagick-with-nsjail/
-

[ Tools ] A Qt and C++ GUI for radare2 reverse engineering framework: https://github.com/radareorg/cutter
-

[ WirelessSecurity ] Coredy CX-E120 Repeater 被发现存在两处安全漏洞: https://blogs.securiteam.com/index.php/archives/3556