腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Android ] Android: RKP Memory Corruption via "rkp_set_init_page_ro" https://bugs.chromium.org/p/project-zero/issues/detail?id=984
" Samsung: RKP Memory Corruption via "rkp_set_init_page_ro": https://t.co/GNjYcLFazY"
-

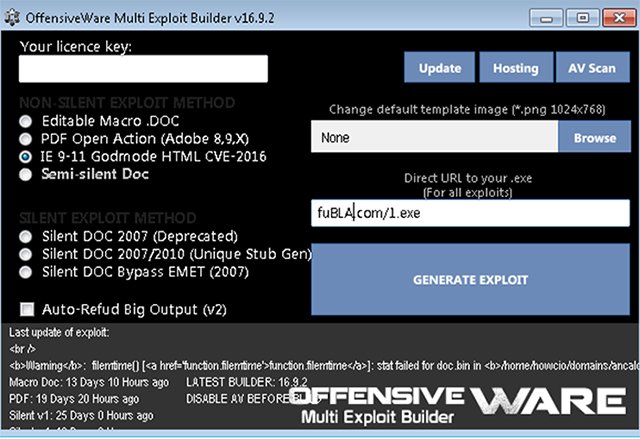
[ Browser ] New paper: The journey and evolution of God Mode in 2016: CVE-2016-0189 https://www.virusbulletin.com/virusbulletin/2017/01/journey-and-evolution-god-mode-2016-cve-2016-0189/ https://t.co/2YR5NUxUdY
" 2016 年 'God Mode' 的演化历程︰ IE VBScript CVE-2016-0189: https://t.co/GWtAEgoGeH https://t.co/2YR5NUxUdY"
-

[ Bug Bounty ] Annual Google VRP Blog is out! https://security.googleblog.com/2017/01/vulnerability-rewards-program-2016-year.html
" Google VRP(漏洞奖励项目) 2016 年总结: https://t.co/UWCtwen3PE"
-

[ Fuzzing ] Fuzzing results for various interpreters. https://github.com/dyjakan/interpreter-bugs
" 研究员 Andrzej Dyjak 对 PHP/Python 等解释器的 Fuzz 结果: https://t.co/iJFWSC27Do"
-

[ iOS ] Ian Beer's exploit for CVE-2017-2370 (kernel memory r/w on iOS 10.2): https://bugs.chromium.org/p/project-zero/issues/detail?id=1004
"iOS/MacOS 用户态指针被内核当作长度处理(CVE-2017-2370): https://t.co/Bw6dmviTzz"
-

[ Linux ] Three of the vulnerabilities fixed were branded “medium” severity by #OpenSSL #Ubuntu #Linux https://threatpost.com/latest-ubuntu-update-includes-openssl-fixes/123513/ via @ threatpost
" Ubuntu 上周发布安全更新,其中包括 3 个 OpenSSL 的中危漏洞: https://t.co/RI21YrGhq1"
-

[ Malware ] MBR勒索木马再度来袭:GoldenEye分析 http://www.freebuf.com/articles/system/124134.html
"MBR勒索木马再度来袭:GoldenEye分析: https://t.co/YovSxhn7T8"
-

[ OpenSourceProject ] Microsoft.VisualStudio.Threading is now OSS under the MIT license. https://github.com/microsoft/vs-threading
"跨平台库 Microsoft.VisualStudio.Threading 开源了: https://t.co/TLxwASPCsh"
-

[ Others ] GitLab deleted some of your data, accidentally that is https://docs.google.com/document/d/1GCK53YDcBWQveod9kfzW-VCxIABGiryG7_z_6jHdVik/pub
"GitLab 不小心删除数据库事件的经过: https://t.co/GxKd9AjcBQ 不想看英文的,可以阅读酷壳上的这篇文章: http://coolshell.cn/articles/17680.html "
-

[ Others ] New Blog Post: Hacking Guatemala’s DNS – Spying on Active Directory Users By Exploiting a TLD Misconfiguration https://t.co/ZEiyCXH1Rp
" Hacking 危地马拉的 DNS — 利用错误配置的 TLD 监视 Active Directory 用户: https://t.co/ZEiyCXH1Rp"
-

[ Others ] Here are our slides from #reconbrx (cc @ coldshell) https://drive.google.com/open?id=0B7tZ-FlDxlt8RE5nSVlIdlJiSFk https://twitter.com/binitamshah/status/826092521684078599
"grap - 定义和匹配二进制程序中的图模型,来自 RECon 会议: https://t.co/Lzv1V9qe6w https://t.co/UC1qKIFqVw"
-

[ Others ] 安全客2016年刊—汇聚全年安全圈优秀技术文章 http://bobao.360.cn/download/book/security-geek-2016-A.pdf http://bobao.360.cn/download/book/security-geek-2016-B.pdf
"安全客 2016 年刊 — 汇聚全年安全圈优秀技术文章: https://t.co/L56w7LFZ7b https://t.co/HhVdGhOn0F"
-

[ Web Security ] Time to patch your Jenkins again: https://wiki.jenkins-ci.org/display/SECURITY/Jenkins+Security+Advisory+2017-02-01
"Java jenkins 2 月份的安全公告︰ https://t.co/hDPLRlL32s"
-

[ Windows ] [Interesting Read] Abusing native Windows functions for shellcode execution http://ropgadget.com/posts/abusing_win_functions.html
" 滥用带有 callback 参数的 Windows Native API 实现 Shellcode 的执行: https://t.co/Y3HVw8vntw "