腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Android ] Android Accessibility Security Report http://blogs.360.cn/360mobile/2016/09/07/research_of_accessibility/ (Chinese)
" Android Accessibility 安全性研究报告,来自 360 移动安全团队: https://t.co/RAK84BquXa "
-

[ Android ] @ ScottyBauer1 @ sagikedmi @ fisher_the_cell I put the poc of cve-2016-3866 in github https://github.com/jiayy/android_vuln_poc-exp cause it had been disclosed
" Android CVE-2016-3866 的 PoC: https://t.co/0f1NEUrWqx "
-

[ Android ] #KCON 2016 Attack Android App's Third Library by dragonltx & quhe https://github.com/knownsec/KCon/raw/master/2016/%5BKCon%202016%5D0827_7_dragonltx_quhe_Attack%20Android%20App's%20Third%20Library.pdf
" 攻击 Android APP 的第三方库,来自 KCon 2016 会议: https://t.co/1XXZkUFj34 "
-

[ Android ] #KCON 2016 Binder Fuzz based on drozer by 行之 @ 0xr0ot https://github.com/knownsec/KCon/raw/master/2016/%5BKCon%202016%5D0827_8_%E8%A1%8C%E4%B9%8B_Binder%20Fuzz%20based%20on%20drozer.pdf
"基于 drozer 的 Android Binder Fuzz,来自 KCon 2016 会议: https://t.co/8j6JNunqNY KCon 2016 会议所有的 PPT: https://github.com/knownsec/KCon/tree/master/2016 "
-

[ Android ] Project Zero blog: "Return to libstagefright: exploiting libutils on Android" by Mark Brand - http://goo.gl/OYU1Ll
" Return to libstagefright: exploiting libutils on Android,来自 Project Zero: https://t.co/rFZOsRq8mj"
-

[ Android ] Banking Trojan, Gugi, evolves to bypass Android 6 protection https://securelist.com/blog/mobile/75971/banking-trojan-gugi-evolves-to-bypass-android-6-protection/
"银行木马 Gugi 可绕过 Android 6 新加的两种安全保护特性: https://t.co/AmqzmfLXyH"
-

[ Android ] APK Signature Scheme v2 - Android 7.0 https://source.android.com/security/apksigning/v2.html
" Android 7.0 版本新引入的 APK 签名方案: https://t.co/uu2I1FbUbn"
-

[ Android ] Android Security Analysis: Final Report https://www.mitre.org/sites/default/files/publications/pr-16-0202-android-security-analysis-final-report.pdf
" 来自 MITRE 的 Android 安全性分析报告: https://t.co/nQsBurojLn"
-

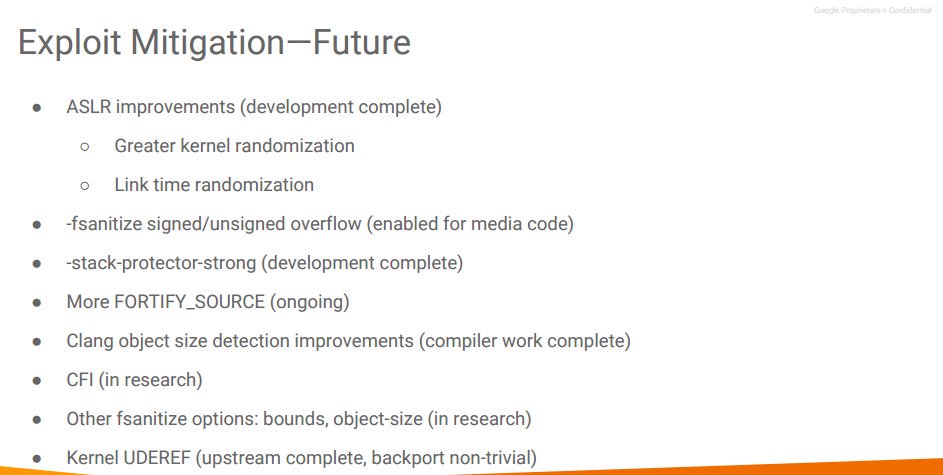
[ Android ] Android Bootcamp 2016. "Defense in depth efforts" presentation (header may not be correct) http://static.googleusercontent.com/media/source.android.com/en//security/reports/Android-Bootcamp-2016-Defense-in-depth-efforts.pdf https://t.co/1AIOpRlSrC
"Android Exploit 深度防御的现在和未来,来自 Android 训练营会议: https://t.co/m8aASk3HpF "
-

[ Attack ] Buckeye cyberespionage group shifts gaze from US to Hong Kong http://www.symantec.com/connect/ko/blogs/buckeye-cyberespionage-group-shifts-gaze-us-hong-kong
"Buckeye 间谍组织将目光从美国转移到香港: https://t.co/AbM2tNyTgN"
-

[ Detect ] Detect botnet spikes using recurrent neural networks with LSTM in our latest blog post by @ dvidrdgz! https://blog.opendns.com/2016/09/06/dominos-botnets-little-lstm/
" 使用递归神经网络的方法检测 Botnet 的峰值: https://t.co/VYbysnkg7b"
-

[ Industry News ] RSA now under DELL , http://blogs.rsa.com/a-new-beginning/
" 从今天开始,RSA 成了戴尔团队的一部分: https://t.co/UjVwtSciGk"
-

[ macOS ] Just posted "The Missing Piece – Sophisticated OS X Backdoor Discovered" (cross-platform) #malware #apple #osx #blog https://securelist.com/blog/research/75990/the-missing-piece-sophisticated-os-x-backdoor-discovered/
" 丢失的片段 - 复杂的 OS X Mokes 后门分析: https://t.co/9eXQqScmox"
-

[ Malware ] 分享一款失败的国产加密勒索软件 http://blogs.360.cn/360safe/2016/09/07/failedransomeware/
"分享一款失败的国产加密勒索软件,来自 360 安全团队: https://t.co/x7KLW22cnI"
-

[ Malware ] #KCON 2016 与僵尸网络攻防对抗的激情岁月 by b1t https://github.com/knownsec/KCon/raw/master/2016/%5BKCon%202016%5D0828_9_b1t_%E4%B8%8E%E5%83%B5%E5%B0%B8%E7%BD%91%E7%BB%9C%E6%94%BB%E9%98%B2%E5%AF%B9%E6%8A%97%E7%9A%84%E6%BF%80%E6%83%85%E5%B2%81%E6%9C%88.pdf
" 与僵尸网络攻防对抗的激情岁月,来自 KCon 2016 会议: https://t.co/rQOnXIf623"
-

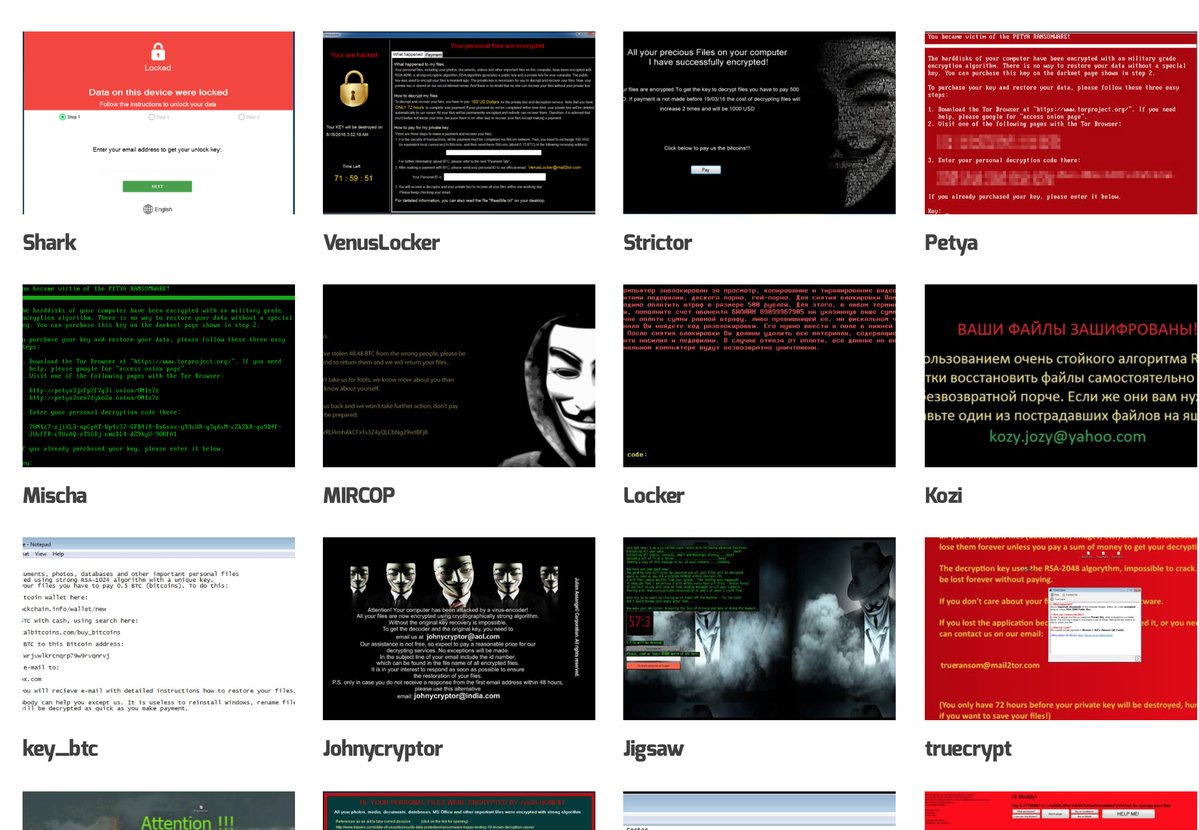
[ Malware ] A nice collection of ransomware notes. http://ransomwareprevention.com/ransomware-notes/ https://t.co/n6xPHE6tBf
" 勒索软件收集笔记: https://t.co/Nv0ru883iY "
-

[ Malware ] 色情应用暗藏杀机,宅男福利竟成“灾难降临” http://blog.avlsec.com/2016/08/3661/sextrap/
" 色情应用暗藏杀机,宅男福利竟成 '灾难降临',来自安天实验室: https://t.co/ErusIP8B3P"
-

[ Network ] Read research on attacking Network Management Systems over the SNMP. http://r-7.co/2cBcBbQ
" 基于 SNMP 攻击网络管理系统的研究,来自 Rapid7,多个网络管理系统的多个漏洞披露: https://t.co/IZ5LtTArX1"
-

[ NetworkDevice ] #KCON 2016 网络设备漏洞分析技术研究 by timo https://github.com/knownsec/KCon/raw/master/2016/%5BKCon%202016%5D0828_6_timo_%E7%BD%91%E7%BB%9C%E8%AE%BE%E5%A4%87%E6%BC%8F%E6%B4%9E%E5%88%86%E6%9E%90%E6%8A%80%E6%9C%AF%E7%A0%94%E7%A9%B6.pdf
" 网络设备漏洞分析技术研究,来自 KCon 2016 会议: https://t.co/FwniJJNGJs"
-

[ Others ] #KCON 2016 剑走偏锋之 Hacking 无处不在 by 朱利军 https://github.com/knownsec/KCon/raw/master/2016/%5BKCon%202016%5D0828_1_%E6%9C%B1%E5%88%A9%E5%86%9B_%E5%89%91%E8%B5%B0%E5%81%8F%E9%94%8B%E4%B9%8B%20Hacking%20%E6%97%A0%E5%A4%84%E4%B8%8D%E5%9C%A8.pdf
" 剑走偏锋之 Hacking 无处不在,来自 KCon 2016 会议: https://t.co/BDbVHQxcGP"
-

[ Others ] #KCON 2016 伪基站高级利用技术 by Seeker https://github.com/knownsec/KCon/raw/master/2016/%5BKCon%202016%5D0828_3_Seeker_%E4%BC%AA%E5%9F%BA%E7%AB%99%E9%AB%98%E7%BA%A7%E5%88%A9%E7%94%A8%E6%8A%80%E6%9C%AF.pdf
" 伪基站高级利用技术,来自 KCon 2016 会议: https://t.co/jlZ4aTLbkh"
-

[ Others ] #KCON 2016 塔防模型落地之运维大战情报 by 黑客叔叔 https://github.com/knownsec/KCon/raw/master/2016/%5BKCon%202016%5D0827_2_%E9%BB%91%E5%AE%A2%E5%8F%94%E5%8F%94_%E5%A1%94%E9%98%B2%E6%A8%A1%E5%9E%8B%E8%90%BD%E5%9C%B0%E4%B9%8B%E8%BF%90%E7%BB%B4%E5%A4%A7%E6%88%98%E6%83%85%E6%8A%A5.pptx
" 塔防模型落地之运维大战情报,来自 KCon 2016 会议: https://t.co/wub3rdafYK"
-

[ Others ] How Spoofing An Ethernet Adapter Lets You Sniff PC Credentials http://www.zdnet.com/article/how-spoofing-an-ethernet-adaptor-lets-you-sniff-pc-credentials/
"如何通过 USB 以太网适配器从锁屏的 PC 上 Sniff 凭据信息: https://t.co/cwOtxsIOPO"
-

[ Others ] Expanding on a Known Vulnerability: Attacking with Jython https://www.tenable.com/blog/expanding-on-a-known-vulnerability-attacking-with-jython
" 用 Jython 攻击一个 JBOSS 老漏洞(CVE-2016-3737): https://t.co/MFFXVTb15V"
-

[ Others ] Keeping Android safe: Security enhancements in Nougat - http://android-developers.blogspot.com.es/2016/09/security-enhancements-in-nougat.html
" Android 7.0 Nougat 版本在安全性方面的提高: https://t.co/cTEE99ThMs"
-

[ Pentest ] #DeepSec 2016 Talk: #badGPO - Using #GPOs for Persistence and Lateral Movement … http://wp.me/p6PE4U-G3 #PowerShell
" badGPO - 利用 GPOs 实现持久渗透和横向移动,来自 DeepSec 会议: https://t.co/6riLf9yU3O "
-

[ Pentest ] Discovering Entry Points http://resources.infosecinstitute.com/discovering-entry-points/
" 攻击行动中,黑客常常使用的'入口点': https://t.co/HeXatfaPxt"
-

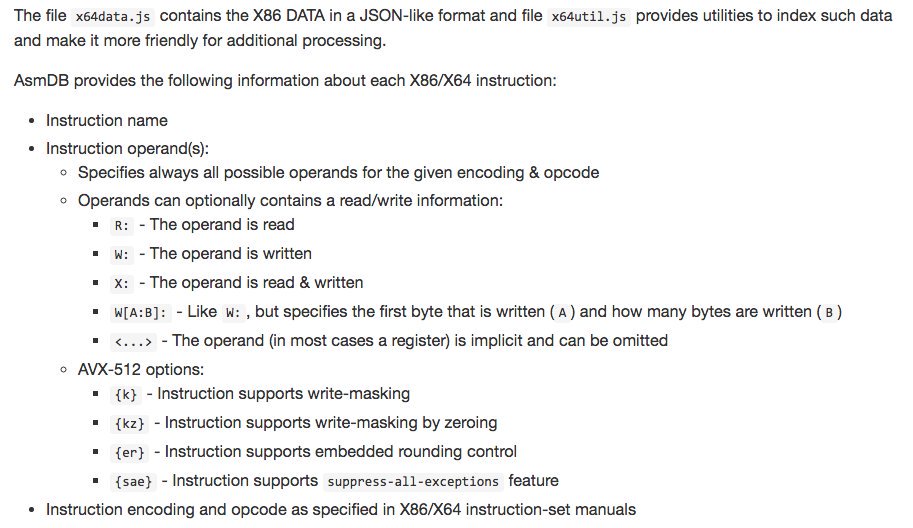
[ Popular Software ] Public domain database of complete x86/x64 instruction set, from legacy to AVX-512 [JS/JSON] https://github.com/asmjit/asmdb https://t.co/yuLhtgDn30
" 完整的 x86/x64 指令集数据库: https://t.co/muKXLVmHSG "
-

[ ReverseEngineering ] #KCON 2016 Reverse Engineering Trilogy by 刘凯仁 @ kaijern https://github.com/knownsec/KCon/raw/master/2016/%5BKCon%202016%5D0827_5_%E5%88%98%E5%87%AF%E4%BB%81_Reverse%20Engineering%20Trilogy.pdf
" 逆向的三大工具:Unicorn、Capstone、Keystone,来自 KCon 2016 会议: https://t.co/CYvM21IfIW "
-

[ ReverseEngineering ] #KCON 2016 VMProtect 的一次奇妙之旅 by 何潇潇 https://github.com/knownsec/KCon/raw/master/2016/%5BKCon%202016%5D0827_6_%E4%BD%95%E6%BD%87%E6%BD%87_VMProtect%20%E7%9A%84%E4%B8%80%E6%AC%A1%E5%A5%87%E5%A6%99%E4%B9%8B%E6%97%85.pdf
" VMProtect 的一次奇妙之旅,来自 KCon 2016 会议: https://t.co/zp89gFOQ0y"
-

[ SCADA ] #KCON 2016 感知、诱捕、情报、协作:网络空间工控系统威胁情报 by Kimon https://github.com/knownsec/KCon/raw/master/2016/%5BKCon%202016%5D0828_8_Kimon_%E6%84%9F%E7%9F%A5%E3%80%81%E8%AF%B1%E6%8D%95%E3%80%81%E6%83%85%E6%8A%A5%E3%80%81%E5%8D%8F%E4%BD%9C%EF%BC%9A%E7%BD%91%E7%BB%9C%E7%A9%BA%E9%97%B4%E5%B7%A5%E6%8E%A7%E7%B3%BB%E7%BB%9F%E5%A8%81%E8%83%81%E6%83%85%E6%8A%A5.pdf
" 感知、诱捕、情报、协作:网络空间工控系统威胁情报,来自 KCon 2016 会议: https://t.co/jzCYwf53Yr"
-

[ Tools ] I forked PartitionAlloc as a stand alone library, added hardening, and wrote a simple C API https://github.com/struct/HardenedPartitionAlloc - It needs your help
" Android Blink 引擎 PartitionAlloc 内存管理器的独立移植版: https://github.com/struct/HardenedPartitionAlloc 通过简单的 C 语言 API 就可以直接使用 "
-

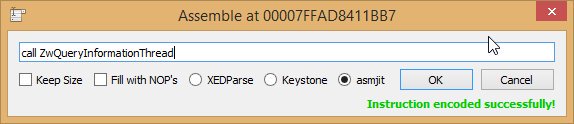
[ Tools ] x64dbg now supports asmjit as a new assembler engine! https://github.com/asmjit #x64dbg #infosec https://t.co/93zvyTcyZ4
"x64dbg 调试器支持 asmjit 作为汇编引擎了: https://t.co/JiCv2S7HOf https://github.com/asmjit/asmjit"
-

[ Tools ] Interactive C# Scripting. Great way to learn the language Essential .NET - C# Scripting https://msdn.microsoft.com/en-us/magazine/mt614271.aspx
"交互式 C# 脚本执行环境: https://t.co/tHq8Desw3i"
-

[ Windows ] [Blog Post] Shellcode Via JScript / VBScript - Happening Now! http://subt0x10.blogspot.com/2016/09/shellcode-via-jscript-vbscript.html Feedback Welcome!
" 基于 DynamicWrapperX,通过 JScript/VBScript 调用 Win32 API 和 Shellcode: https://t.co/zmKlxOeL0v "
-

[ WirelessSecurity ] #KCON 2016 无线 Fuzzing 之旅 by Kevin2600 https://github.com/knownsec/KCon/raw/master/2016/%5BKCon%202016%5D0828_2_Kevin2600_%E6%97%A0%E7%BA%BF%20Fuzzing%20%E4%B9%8B%E6%97%85.pdf
" 无线 Fuzzing 之旅,来自 KCon 2016 会议: https://t.co/Ed8qCXWcIe"