腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Attack ] M-Trends Asia Pacific: Organizations Must Improve at Detecting and Responding to Breaches https://www.fireeye.com/blog/threat-research/2016/08/m-trends_asia_pacifi.html
"FireEye 发布的 《2016 年亚太地区安全趋势报告》: https://t.co/q55vhqLLMj"
-

[ Attack ] Here are 2016’s most prominent breaches and security incidents so far: http://bit.ly/2be7OYp https://t.co/7apFKkMkY1
" 趋势科技的 2016 年年中报告:勒索软件统治世界︰ https://t.co/HhqplvAHkK "
-

[ Attack ] NEW REPORT: “The Million Dollar Dissident: NSO Group’s iPhone Zero-Days used against a UAE Human Rights Defender” https://citizenlab.org/2016/08/million-dollar-dissident-iphone-zero-day-nso-group-uae/
" 一家位于以色列的公司 NSO Group 向政府出售 Pegasus 软件,利用 3 个 iPhone 0Day 攻击阿联酋人权捍卫者: https://t.co/97YSkWM0xG 详细的报告: https://info.lookout.com/rs/051-ESQ-475/images/lookout-pegasus-technical-analysis.pdf "
-

[ Attack ] Threat Intelligence Report for the Telecommunications Industry - Securelist https://securelist.com/analysis/publications/75846/threat-intelligence-report-for-the-telecommunications-industry/
" 电信行业的威胁情报报告,来自卡巴斯基: https://t.co/DarWjWN6Ep "
-

[ Cloud ] Azure 0day Cross-Site Scripting with Sandbox Escape https://www.securesolutions.no/guest-blog-at-pen-testing-sans-org-azure-0day-cross-site-scripting-with-sandbox-escape/
"微软 Azure 云平台的一枚 XSS 0Day,可以实现跨站点的 XSS: https://t.co/XvBdSuD8Ed"
-

[ Conference ] #HITBGSEC #CommSec LIVE STREAM: https://www.youtube.com/watch?v=EODWYP0z58g - Slides are here: http://gsec.hitb.org/materials/sg2016/ (RTs greatly appreciated)
" HITB GSEC 会议的 PPT 可以下载了: http://gsec.hitb.org/materials/sg2016/ "
-

[ iOS ] Greetings from SG! #HITBGSEC Presentation, and a new SBTool to inspect #iOS/#MacOS #sandbox: http://newosxbook.com/articles/hitsb.html https://t.co/vwTX2QYwqI
" Hack in the Apple (sand)Box: http://newosxbook.com/articles/hitsb.html PPT: http://newosxbook.com/files/HITSB.pdf "
-

[ iOS ] iOS 9.3.5: WebKit RCE & kernel privilege escalation… upgrade now now now https://support.apple.com/en-gb/HT207107
"iOS 9.3.5 发布,修复了一个 WebKit RCE 漏洞以及两个内核漏洞: https://t.co/Eg0qYWST9G"
-

[ Linux ] Great implementation of CVE-2016-5696 TCP Session RST or Hijacking by @ jduck: https://github.com/jduck/challack
" Joshua J. Drake 也为 Linux Off-Path TCP 流量劫持漏洞(CVE-2016-5696) 写了一个 PoC: https://t.co/DAsdr3CET9"
-

[ Linux ] My "State of the Kernel Self Protection Project" slides from the Linux Security Summit: https://outflux.net/slides/2016/lss/kspp.pdf
" (Linux)内核自我防护项目的现状,来自 Linux 安全峰会︰ https://t.co/SCPSadIYlg"
-

[ Malware ] Alma Ransomware: Analysis of a New Ransomware Threat (and a decrypter!) https://info.phishlabs.com/blog/alma-ransomware-analysis-of-a-new-ransomware-threat-and-a-decrypter
" Alma - 一款新的勒索软件,来自 PhishLabs: https://t.co/g4ZVwWb7s0"
-

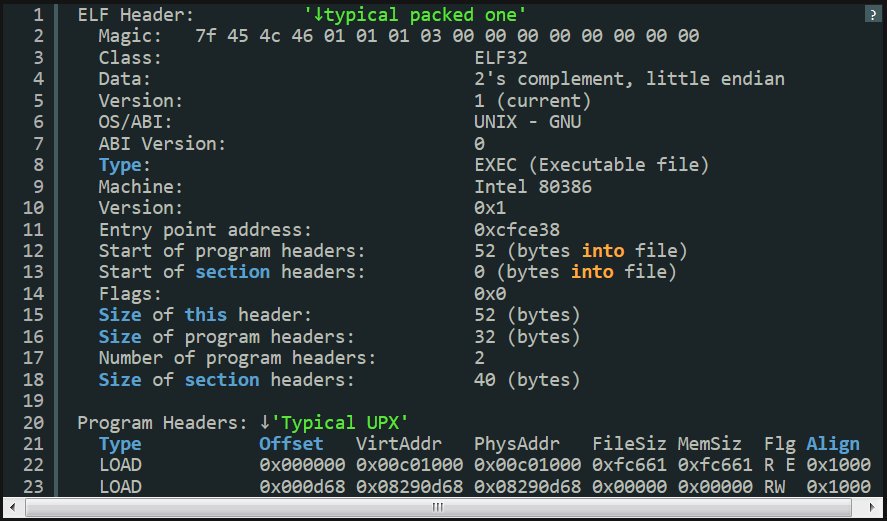
[ Malware ] MMD-0055-2016 - Linux/PnScan ; #ELF worm that still circles around. http://blog.malwaremustdie.org/2016/08/mmd-0054-2016-pnscan-elf-worm-that.html Via @ MalwareMustDie. https://t.co/GI4n8O3Jdk
" Linux/PnScan ELF 蠕虫病毒分析: http://blog.malwaremustdie.org/2016/08/mmd-0054-2016-pnscan-elf-worm-that.html "
-

[ Malware ] My new post for @ Malwarebytes "Unpacking the #spyware disguised as antivirus": https://blog.malwarebytes.com/threat-analysis/2016/08/unpacking-the-spyware-disguised-as-antivirus/ //#KorplugRAT
" 一款伪装成 McAfee 反病毒软件的间谍软件分析,来自 MalwareBytes: https://t.co/Bke0kYRfbf "
-

[ Network ] How the Consumer Product Safety Commission is (Inadvertently) Behind the Internet’s Largest DDoS Attacks https://blog.cloudflare.com/how-the-consumer-product-safety-commission-is-inadvertently-behind-the-internets-largest-ddos-attacks/
" 互联网最大的 DDoS 攻击背后的消费者产品安全委员会: https://t.co/7srDxp37Vm"
-

[ Obfuscation ] Protecting Software through Obfuscation: Can It Keep Pace with Progress in Code Analysis? http://www.cs.rhul.ac.uk/home/kinder/papers/csur16-obfuscation.pdf
" 代码混淆技术可以跟上代码分析技术的发展步伐吗,Paper: https://t.co/YXyChvQ3XV"
-

[ Others ] By analysing how FINGERS interact w/WiFi signals, #InfoSec researchers accurately recover 93.5+% of all keystrokes. https://www.sigmobile.org/mobicom/2015/papers/p90-aliA.pdf
" 有研究员通过分析手指移动对 WiFi 信号的影响,还原按键信息,准确率达 93.5%+: https://www.sigmobile.org/mobicom/2015/papers/p90-aliA.pdf "
-

[ Others ] Hacking Soft Tokens - Advanced Reverse Engineering on Android http://gsec.hitb.org/materials/sg2016/whitepapers/Hacking%20Soft%20Tokens%20-%20Bernhard%20Mueller.pdf
" Hacking Soft Tokens 与 Android 高级逆向,来自 HITB GSEC 会议: https://t.co/XeOF1IzyWx"
-

[ Others ] New blog post: "How many x86 instructions are there?" https://fgiesen.wordpress.com/2016/08/25/how-many-x86-instructions-are-there/ It's surprisingly tricky to answer meaningfully.
" 到底有多少条 x86 指令: https://t.co/4SG349Urpb "
-

[ Tools ] We have two code releases for you today! Windows Intel Processor Trace Driver https://github.com/talos-vulndev/TalosIntelPtDriver and FuzzFlow https://github.com/talos-vulndev/FuzzFlow
" Talos 公开了两个项目, Intel 处理器跟踪驱动: https://t.co/FD433CGZpJ FuzzFlow: https://t.co/isTrrvbnNF"
-

[ Tools ] #Python application to reverse engineering http://buff.ly/2bitcMK #infosec #security #re
" 有一些工具会将 Python 代码转换成可执行文件, pyThaw 这个工具则用于从可执行文件中还原脚本: https://t.co/tXJLqWDl1g "
-

[ Tools ] Introducing vcsmap: a plugin-based tool to scan public version control systems for sensitive information. http://vcsmap.org/
" vcsmap - 从 GitHub 中扫描敏感信息泄漏的工具: https://t.co/b75DTqKwqW"
-

[ Web Security ] The Mozilla Observatory is handy for spot-checking common web server configuration issues: https://observatory.mozilla.org
" Mozilla Observatory - Web 服务器安全配置在线扫描工具︰ https://t.co/oPZXJ6HZBa"
-

[ Windows ] Getting Physical: Extreme abuse of Intel based Paging Systems – Part 3 – Windows HAL’s Heap https://blog.coresecurity.com/2016/08/25/getting-physical-extreme-abuse-of-intel-based-paging-systems-part-3-windows-hals-heap/
" 英特尔分页系统的极端滥用 Part 2 - 剖析 Windows HAL 堆: https://t.co/BWlFWmHtyS"
-

[ Windows ] I never knew that .NET could be manually loaded from C/C++. http://www.ownedcore.com/forums/world-of-warcraft/world-of-warcraft-bots-and-programs/wow-memory-editing/320083-guide-loading-net-4-0-clr.html - The dll can be dumped & then analyzed in dnspy
" 自己写代码加载 .NET 运行时库: https://t.co/0YVh5MROSh-dll "
-

[ Windows ] Windows Update borks PowerShell – Microsoft won't fix it for a week http://m.theregister.co.uk/2016/08/25/microsoft_breaks_powershell_with_borked_update_wont_fix_it_for_a_week/
"最近的 Windows 补丁更新破坏了一项关键特性 - PowerShell,有一周了: https://t.co/q10UA7VkSP"
-

[ Windows ] Data Driven Software Security - recap on new mitigations in windows 10 AU - http://gsec.hitb.org/materials/sg2016/COMMSEC%20D1%20-%20Sweety%20Chauhan%20-%20Data%20Driven%20Software%20Security.pdf
"数据驱动的软件安全与 Windows 10 中的新缓解技术: https://t.co/SQzOzMZjUl"
-

[ Windows ] Just posted an @ SS_WarRoom blog on my analysis of MS16-098 complete with a BSOD inducing PoC https://warroom.securestate.com/an-analysis-of-ms16-098/
" MS16-098 win32k 漏洞的分析与 PoC: https://t.co/hk6OPjE9EC "