腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Attack ] 通过粘贴可以利用 .NET 方法中的反序列化问题分析 : https://www.nccgroup.trust/uk/about-us/newsroom-and-events/blogs/2018/december/beware-of-deserialisation-in-.net-methods-and-classes-code-execution-via-paste/
-

[ Browser ] ZDI 对 Pwn2Own 2018 Microsoft Edge 漏洞(CVE-2018-8179)的详细分析: https://www.zerodayinitiative.com/blog/2018/12/17/seeing-double-exploiting-a-blind-spot-in-memgc
-

[ Bug Bounty ] 从 Self XSS 到存储型 XSS 的漏洞挖掘: https://nahoragg.github.io/bugbounty/2018/12/15/Self-XSS-to-Interesting-Stored-XSS.html
-

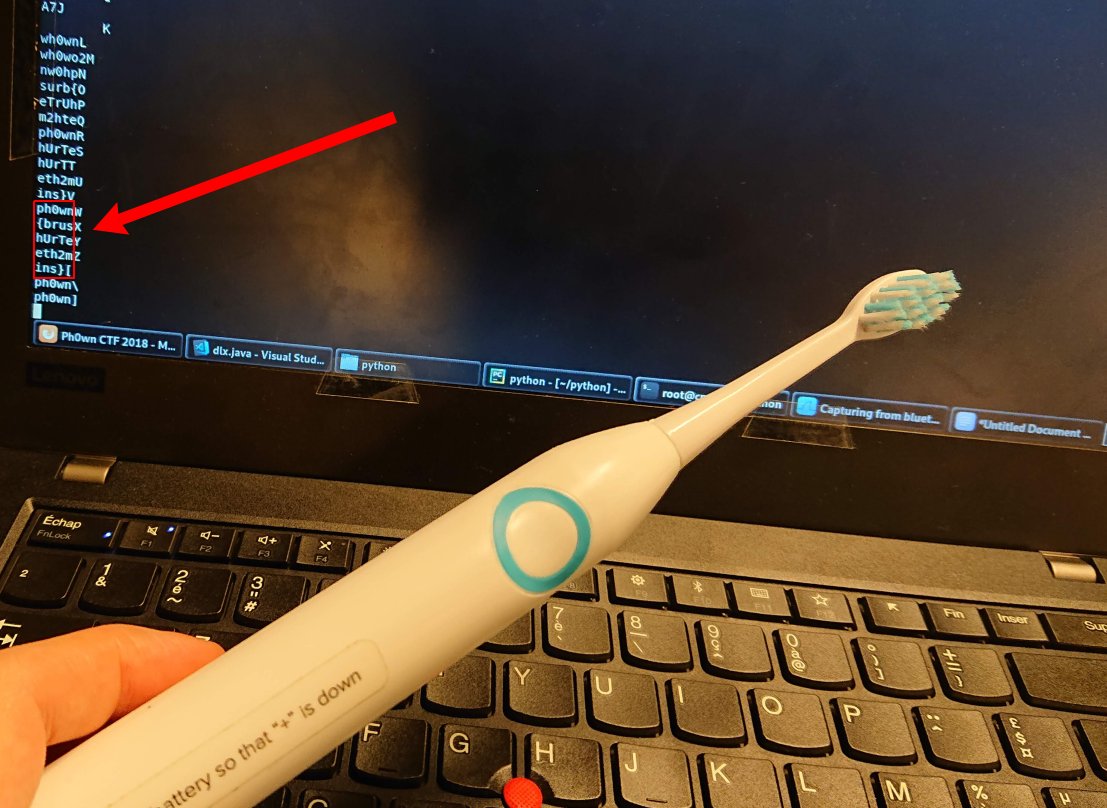
[ Challenges ] Ph0wn 2018 CTF Healing the Toothbrush 挑战 : https://twitter.com/cn0Xroot/status/1074545684383068160/photo/1
-

[ Fuzzing ] Redqueen - Fuzzing with Input-to-State Correspondence,一种轻量级有效的污点跟踪和基于符号执行的 Fuzzing : https://www.syssec.ruhr-uni-bochum.de/media/emma/veroeffentlichungen/2018/12/17/NDSS19-Redqueen.pdf
-

[ iOS ] iOS/macOS 内核 task_inspect 信息泄漏漏洞披露(CVE-2018-4431): https://blogs.securiteam.com/index.php/archives/3802
-

[ Linux ] Linux Userland 下的内存 shellcode 注入: https://blog.sektor7.net/#!res/2018/pure-in-memory-linux.md
-

[ Linux ] Linux __rcu_read_unlock 中的 Crash: https://groups.google.com/forum/#!topic/syzkaller-bugs/HoRZMT92WKk
-

[ Malware ] Charming Kitten 回归 - 由伊朗国家支持的最新一波网络钓鱼攻击分析: https://blog.certfa.com/posts/the-return-of-the-charming-kitten/
-

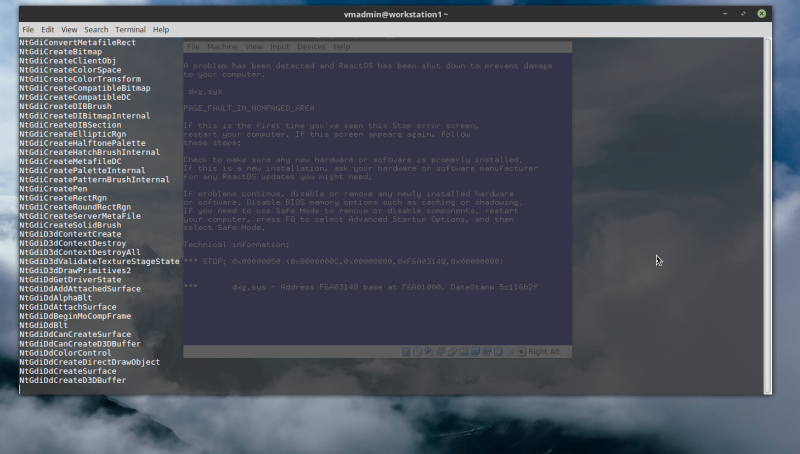
[ Others ] 让 ReactOS 再次伟大 Part 1 - 使用 ROCALL 寻找系统中的 BSOD 错误: http://www.kernelmode.info/forum/viewtopic.php?f=11&t=5302
-

[ Tools ] Carnegie Mellon 二进制分析平台的经验(CMU BAP): http://www.s3.eurecom.fr/~aurel/GT_SSL/Thomas_BAP%20Presentation.pdf
-

[ Tools ] docx-embeddedhtml-injection - Microsoft Word 2016 通过内嵌视频下载执行恶意软件的利用脚本: https://github.com/thom-s/docx-embeddedhtml-injection
-

[ Virtualization ] 配置 VMCS 并运行 Guest Code: https://rayanfam.com/topics/hypervisor-from-scratch-part-5/
-

[ Vulnerability ] Ghost 博客系统 XSS 漏洞详情披露: https://dev.to/antogarand/xss-in-ghost-2o6j
-

[ Vulnerability ] Elasticsearch Kibana Console plugin 的本地文件包含漏洞(CVE-2018-17246): https://twitter.com/i/web/status/1074627634150006784
-

[ Windows ] Windows Internals 系列 - Windows 容器: https://insider.windows.com/en-us/articles/windows-internals-series-containers-in-windows/
-

[ Attack ] Kerberoasting - 从安装到破解 : https://medium.com/@markmotig/kerberoasting-from-setup-to-cracking-3e8c980f26e8
-
-
-
-
-

[ Tools ] 使用 Burp Suite 宏自动化处理 Session 会话: https://www.riddhishree.com/posts/automated-session-handling-using-burp-suite-macros/
-

[ Vulnerability ] Apache CouchDB 远程特权提升漏洞(CVE-2018-17188) : https://seclists.org/oss-sec/2018/q4/255