腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Android ] 针对动态逆向 Android 应用的保护方案: http://isyou.info/jowua/papers/jowua-v7n3-3.pdf
-

[ APT ] Sofacy 组织(APT28)的全球活动情况分析: https://researchcenter.paloaltonetworks.com/2018/12/dear-joohn-sofacy-groups-global-campaign/
-

[ APT ] Donot(APT-C-35)组织对在华巴基斯坦商务人士的定向攻击活动分析: https://ti.360.net/blog/articles/donot-group-is-targeting-pakistani-businessman-working-in-china/
-

[ Attack ] 通过 C# 使用 SetWindowHookEx 实现 DLL 注入 : https://github.com/enkomio/shed/blob/master/ES.Shed.ManagedInjector/Injector.cs
-

[ Browser ] WebKit Int32/Double arrays 对象可以有 Proxy 对象在 prototype 链中(CVE-2018-4438): https://bugs.chromium.org/p/project-zero/issues/detail?id=1649
-

[ Bug Bounty ] From blind XXE to root-level file read access,在 BugBounty 中使用的 XXE 盲打利用技巧: https://www.honoki.net/2018/12/from-blind-xxe-to-root-level-file-read-access/
-

[ Exploit ] Binary Exploitation 介绍 : https://errantsecurity.com/2018/12/11/binary-exploitation-background.html
-

[ Forensics ] TeraCopy 取证分析 Part 3: https://www.stark4n6.com/2018/12/teracopy-forensic-analysis-part-3.html Part 2: https://www.stark4n6.com/2018/11/teracopy-forensic-analysis-part-2.html Part 1: https://www.stark4n6.com/2018/11/teracopy-forensic-analysis-part-1.html
-

[ IoTDevice ] 针对物联网设备的僵尸网络分析: https://asert.arbornetworks.com/fast-furious-iot-botnets-regifting-exploits/
-

[ Linux ] Linux/x86 - Bind (1337/TCP) Ncat (/usr/bin/ncat) Shell (/bin/bash) + Null-Free Shellcode (95 bytes): https://www.exploit-db.com/exploits/45980
-

[ MalwareAnalysis ] Operation Fast Cash - Hidden Cobra 使用的 AIX PowerPC 恶意软件解析: https://github.com/fboldewin/FastCashMalwareDissected/blob/master/Operation%20Fast%20Cash%20-%20Hidden%20Cobra%E2%80%98s%20AIX%20PowerPC%20malware%20dissected.pdf
-

[ MalwareAnalysis ] 持续三年攻击俄罗斯石油公司的威胁分析: https://threatvector.cylance.com/en_us/home/poking-the-bear-three-year-campaign-targets-russian-critical-infrastructure.html
-

[ Popular Software ] 通过 Fuzzing Adobe Reader 50 天获得 50 个 CVE: https://research.checkpoint.com/50-adobe-cves-in-50-days/
-

[ Symbolic Execution ] symbolic-execution-tutorial - 基于 angr 框架的符号执行教程: https://github.com/ercoppa/symbolic-execution-tutorial/blob/master/symbolic-execution.pdf
-

[ Tools ] IKOS - 一款基于 Abstract Interpretation 理论的 C/C++ 静态分析器 : https://github.com/NASA-SW-VnV/ikos
-

[ Tools ] ThunderShell - Python / PowerShell 实现的 HTTP 通信的远程控制软件: https://github.com/Mr-Un1k0d3r/ThunderShell
-

[ Tools ] 通过 ee-outliers 和 Elasticsearch 来检测 TLS beaconing : https://blog.nviso.be/2018/12/11/tls-beaconing-detection-using-ee-outliers-and-elasticsearch/
-

[ Tools ] Exchange Online Fiddler 扩展介绍: https://blogs.technet.microsoft.com/exchange/2018/12/11/introducing-the-exchange-online-fiddler-extension/
-

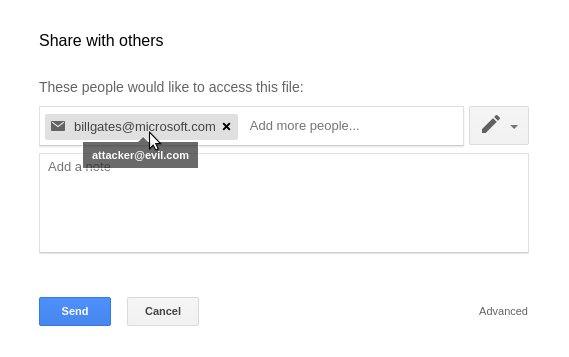
[ Vulnerability ] 我是如何从 Google 窃取你的照片的,3 个 Google 漏洞的赏金报告 - 邀请欺骗/Google Drive 图片窃取/Google Photos 照片分享: https://blog.avatao.com/How-I-could-steal-your-photos-from-Google/
-

[ Vulnerability ] 视频会议的安全风险 - What Didn't Work Out with WhatsApp: https://googleprojectzero.blogspot.com/2018/12/adventures-in-video-conferencing-part-4.html
-

[ Vulnerability ] laravel-poc-CVE-2018-15133 - Laravel APP_KEY 泄露导致的远程代码执行 POC: https://github.com/kozmic/laravel-poc-CVE-2018-15133
-

[ Windows ] Windows Kernel Transaction Manager 中的 0day 漏洞 (CVE-2018-8611) : https://securelist.com/zero-day-in-windows-kernel-transaction-manager-cve-2018-8611/89253/https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8611
-

[ Challenges ] Pwn2Own 2017 Adobe JPEG2000 Heap Overflow Exploit 分析: https://www.zerodayinitiative.com/blog/2018/12/11/when-one-corruption-is-not-enough-analyzing-an-adobe-pwn2own-exploit
-

[ Exploit ] x86 中通过 ROP bypass DEP 保护机制介绍: https://bytesoverbombs.io/bypassing-dep-with-rop-32-bit-39884e8a2c4a
-

[ Forensics ] TorPCAP - Tor 网络取证分析技术: https://www.netresec.com/?page=Blog&month=2018-12&post=TorPCAP---Tor-Network-Forensics
-

[ Pentest ] 如何利用 HQL 注入 : https://medium.com/@SecurityBender/exploiting-a-hql-injection-895f93d06718
-

[ Vulnerability ] Calibre E-Book 服务未授权访问利用: https://blog.chrisbonk.ca/2018/12/knowledge-is-power-exploring-over-1800.html