腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Android ] Android 漏洞 CVE-2018-9365 的 POC : https://github.com/JiounDai/Bluedroid/blob/master/poc_CVE-2018-9365.c
-

[ Bug Bounty ] Microsoft 推出在 Windows 体系中对于身份验证的 Bounty 计划,奖励500-100000 万美元: https://blogs.technet.microsoft.com/msrc/2018/07/17/microsoft-launches-identity-bounty-program/
-

[ Crypto ] 私有数据对象(paper): https://arxiv.org/abs/1807.05686
-

[ Data Breach ] ProCare Health 在未经同意的情况下收集了80万病人的个人资料: https://threatpost.com/800k-patient-records-at-issue-in-procare-health-snafu/134071/:
-

[ Exploit ] 黑客教程之解释缓冲区溢出: https://www.hackingtutorials.org/exploit-tutorials/buffer-overflow-explained-basics/
-

[ Fuzzing ] 使用神经程序学习来实现的有效 Fuzz(paper): https://arxiv.org/abs/1807.05620
-

[ Hardware ] Microhard 3G/4G 网关 CSRF 漏洞 POC: https://www.exploit-db.com/exploits/45034/
-

[ Hardware ] Microhard 3G/4G 网关拒绝服务漏洞 POC : https://www.exploit-db.com/exploits/45035/
-

[ Hardware ] Microhard 3G/4G 网关远程 root 漏洞 POC: https://www.exploit-db.com/exploits/45038
-

[ Hardware ] Microhard 3G/4G网关配置下载漏洞POC: https://www.exploit-db.com/exploits/45036
-

[ Hardware ] Microhard 3G/4G 网关文件访问漏洞 POC: https://www.exploit-db.com/exploits/45037/
-

[ Hardware ] Microhard 3G/4G 网关默认登录凭证 POC : https://www.exploit-db.com/exploits/45040/
-

[ Hardware ] Microhard 3G/4G 网关受限 shell 逃逸 POC: https://www.exploit-db.com/exploits/45041
-

[ IoTDevice ] D-Link DIR-300 CSRF 漏洞披露: http://seclists.org/fulldisclosure/2018/Jul/57
-

[ Linux ] Linux/ARM - Bind Shell Shellcode (104 bytes): https://www.exploit-db.com/exploits/45029/
-

[ Linux ] Linux X64 下的反向shell代码: https://www.exploit-db.com/exploits/45039
-

[ Malware ] KaixinEK 恶意软件利用的漏洞和 POC : https://twitter.com/nao_sec/status/1018821895972536326
-

[ Malware ] Andariel 组织在被攻破的网站上注入 ActiveX 对象侦察脚本,以扩大后期对 ActiveX 漏洞的利用范围: https://threatpost.com/recent-andariel-group-activex-attacks-point-to-future-targets/134053/
-

[ MalwareAnalysis ] ESET 对监控乌克兰政府部门的间谍软件 Vermin RAThole 的深入分析: https://www.welivesecurity.com/2018/07/17/deep-dive-vermin-rathole/
-

[ Others ] PowerView 使用教程系列 Part 5: https://posts.specterops.io/the-powerview-powerusage-series-5-7ca3ebb23927
-

[ Others ] 检测和实现对SAML接口的XXE攻击: https://web-in-security.blogspot.com/2014/11/detecting-and-exploiting-xxe-in-saml.html
-

[ Pentest ] 使用 ELK 协助分析渗透测试情报收集数据: https://www.marcolancini.it/2018/blog-elk-for-nmap/
-

[ Popular Software ] QNAP Q’Center web 管理界面存在多个安全漏洞 : https://threatpost.com/multiple-bugs-found-in-qnap-qcenter-web-console/133884/
-

[ Popular Software ] PayPal 漏洞挖掘,如何暴力穷举所有 SMC 消息 : https://blog.ayoubaitelmokhtar.com/2018/06/paypal-bbp-i-couldve-deleted-all-smc.html
-

[ ReverseEngineering ] 如何开始逆向学习与病毒分析 : https://hshrzd.wordpress.com/how-to-start/
-

[ SecurityAdvisory ] Oracle 发布 7 月重要安全更新 : http://www.oracle.com/technetwork/security-advisory/cpujul2018-4258247.html
-

[ Tools ] OWTF - Offensive Web测试框架: https://github.com/owtf/owtf
-
-

[ Tools ] GTFOBins 项目,收集可被滥用于绕过系统安全限制的 Unix 命令列表: https://gtfobins.github.io/
-

[ Tools ] 使用 Invoke-PWAudit 识别活动目录共享密码: https://www.ubeeri.com/blog/2018/7/16/auditing-shared-passwords-in-active-directory-with-invoke-pwaudit
-

[ Tools ] crossdomain - 一款自动检测跨域错误配置的工具: https://github.com/dienuet/crossdomain
-

[ Tools ] binninja 的 IPython 插件: https://github.com/ernw/binja-ipython
-

[ Tools ] Netflix 云安全团队发布 Diffy 项目:一个用于云环境下数字取证的 Differencing Engine: https://medium.com/@NetflixTechBlog/netflix-sirt-releases-diffy-a-differencing-engine-for-digital-forensics-in-the-cloud-37b71abd2698
-

[ Tools ] microctfs - 小型 CTF 比赛的 docker 镜像: https://github.com/gabemarshall/microctfs
-

[ Tools ] oo7:一款二进制框架,用于检测和分析可以受到Spectre攻击的代码片段 : https://arxiv.org/abs/1807.05843
-

[ Virtualization ] 减少容器攻击面的解决方案: http://www.ibr.cs.tu-bs.de/users/kurmus/papers/kurmus-ndss13.pdf
-

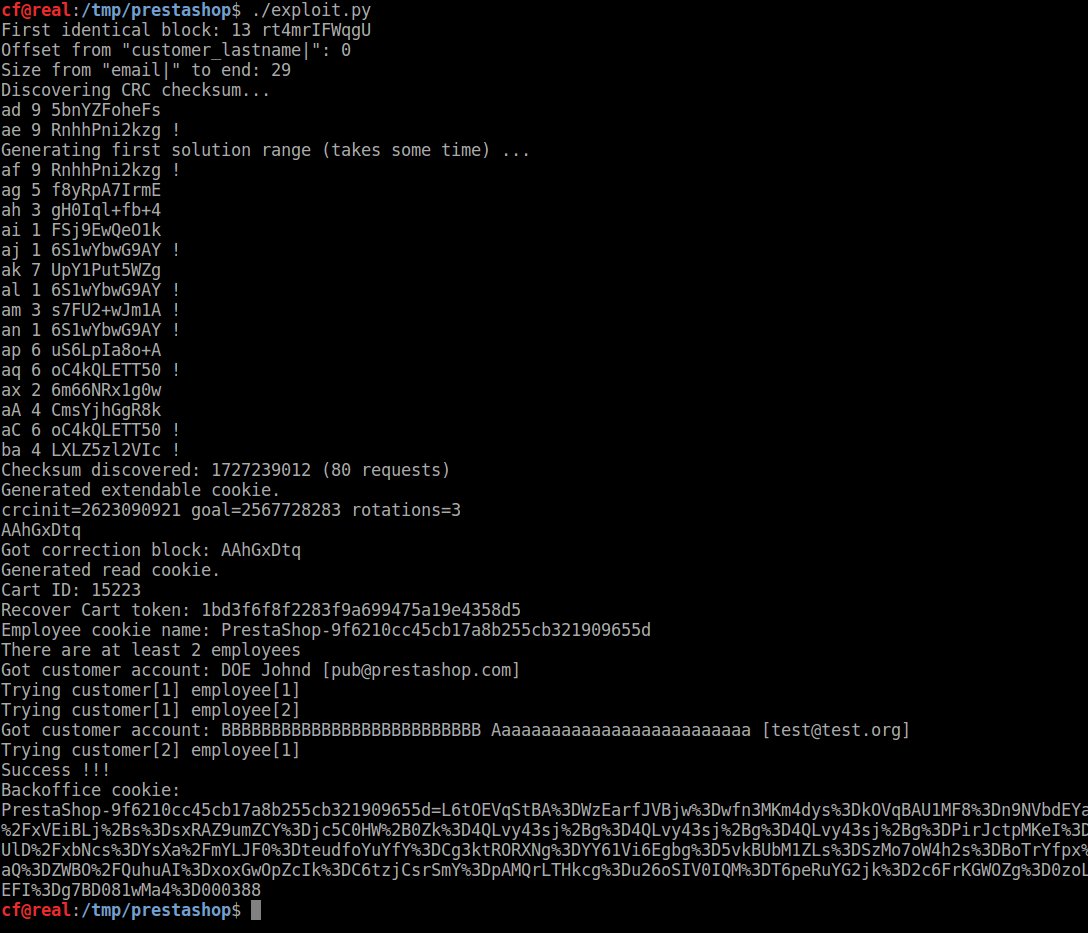
[ Vulnerability ] PrestaShop 1.6.x 权限提升漏洞详情披露(CVE-2018-13784): https://www.ambionics.io/blog/prestashop-privilege-escalation
-

[ Windows ] 对 PE 文件签名的深入研究: http://research32.blogspot.com/2016/03/pe-file-signing.html
-

[ Windows ] 如何为活动目录服务 Active Directory 配置密码黑名单 : https://engineeringblog.yelp.com/2018/04/ad-password-blacklisting.html
-
-

[ Cloud ] AWS EC2 策略安全配置: https://labs.mwrinfosecurity.com/blog/ec2-policies-security-freedom-and-both/
-
-

[ MalwareAnalysis ] Kaspersky 对 Cryakl 勒索软件的追踪与对抗: https://securelist.com/the-return-of-fantomas-or-how-we-deciphered-cryakl/86511/
-