腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Browser ] 剖析现代浏览器漏洞:CVE-2018-8174 案例研究: https://medium.com/@florek/dissecting-modern-browser-exploit-case-study-of-cve-2018-8174-1a6046729890
-

[ Browser ] Pwn2Own 2018 Safari 漏洞利用开发记录系列 Part 4(CVE-2018-4192),详解 JavaScriptCore 漏洞在实战中的高级利用过程: https://blog.ret2.io/2018/07/11/pwn2own-2018-jsc-exploit/
-

[ Linux ] Linux Kernel < 4.13.9 (Ubuntu 16.04/Fedora 27) - 本地提权漏洞EXP(CVE-2017-16995): https://www.exploit-db.com/exploits/45010/
-

[ macOS ] Apple CUPS 打印系统的多个特权提升和沙箱逃逸漏洞: http://blog.gdssecurity.com/labs/2018/7/11/cups-local-privilege-escalation-and-sandbox-escapes.html
-

[ macOS ] 如何访问 macOS 上的锁定文件: https://blog.elcomsoft.com/2018/07/accessing-lockdown-files-on-macos/
-

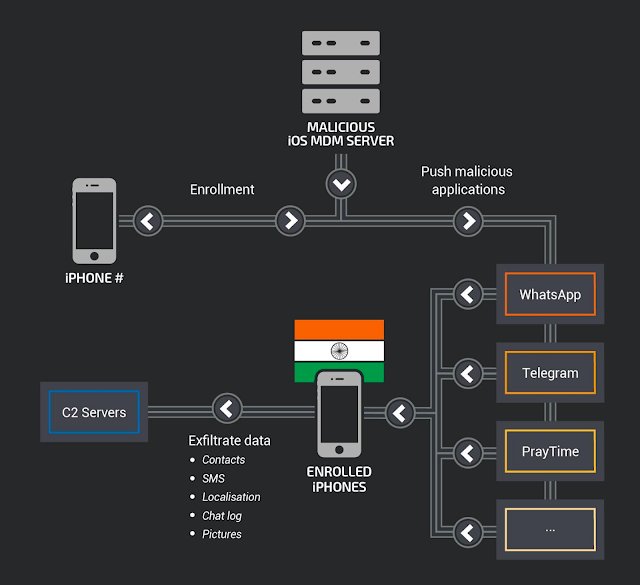
[ MalwareAnalysis ] 针对印度手机用户的高级恶意活动利用 MDM 控制设备: https://blog.talosintelligence.com/2018/07/Mobile-Malware-Campaign-uses-Malicious-MDM.html?
-

[ Others ] 揭露国外势力如何试图在 Twitter 上影响法国选举: https://blog.0day.rocks/uncovering-foreign-trolls-trying-to-influence-french-elections-on-twitter-a78a8c12953
-

[ Others ] Hybrid Analysis 添加新功能,将恶意软件的行为指标映射到 MITRE ATT&CK 框架: https://twitter.com/HybridAnalysis/status/1017066468888981505
-

[ Pentest ] 使用 winrm.vbs 绕过应用白名单执行任意未签名代码: https://posts.specterops.io/application-whitelisting-bypass-and-arbitrary-unsigned-code-execution-technique-in-winrm-vbs-c8c24fb40404
-

[ Popular Software ] LBank 移动端应用中的 tradeRifle 漏洞详情披露(CVE-2018-13363): https://www.peckshield.com/2018/07/12/tradeRifle/
-

[ ReverseEngineering ] 寻找 NES 模拟器中的隐藏功能: https://jamchamb.github.io/2018/07/11/animal-crossing-nes-emulator-hacks.html
-

[ Tools ] 通过 Pwn Adventure 3 游戏学习 FRIDA: https://x-c3ll.github.io/posts/Frida-Pwn-Adventure-3/
-

[ Tools ] NPM 模块 eslint-scope 的所有者账户被入侵,攻击者在模块中嵌入了恶意代码以感染该模块的用户: https://github.com/eslint/eslint-scope/issues/39
-

[ Tools ] Lin.security - 练习 Linux 提权用的虚拟机: https://in.security/lin-security-practise-your-linux-privilege-escalation-foo/
-

[ Vulnerability ] Lenovo SU v5.07 缓冲区溢出漏洞披露(CVE-2018-9063): http://seclists.org/fulldisclosure/2018/Jul/47
-

[ Web Security ] 静态网站需要启用 HTTPS 的原因,来自 Troy Hunt 的探讨: https://www.troyhunt.com/heres-why-your-static-website-needs-https/
-
-
-

[ MalwareAnalysis ] 攻击者通过 Windows 自带工具加载挖矿程序的检测分析: https://redcanary.com/blog/cryptomining-enabled-by-native-windows-tools/
-

[ MalwareAnalysis ] McAfee 发现 Google Play 中存在一种 Android/FoulGoal.A 类型恶意应用,该类应用在后台窃取用户数据并发向远程服务器: https://securingtomorrow.mcafee.com/mcafee-labs/google-play-users-risk-a-yellow-card-with-android-foulgoal-a/
-

[ SecurityReport ] 2018 年中网络攻击趋势报告,来自 checkpoint : https://research.checkpoint.com/cyber-attack-trends-2018-mid-year-report/