腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Browser ] V8 JavaScript 引擎 JS 代码解析(Parsing)、Ignition 与 TurboFan 编译器编译、二进制代码生成、JIT 优化的过程: https://speakerdeck.com/brn/source-to-binary-journey-of-v8-javascript-engine-english-version
-

[ Browser ] V8 引擎为了提高垃圾回收(GC)的效率,减少内存回收时的中断时间,在其并行 GC 管理器 Orinoco 中实现了一个新特性 - Scavenger(清道夫): https://v8project.blogspot.com/2017/11/orinoco-parallel-scavenger.html
-

[ iOS ] iOS 11:iOS 安全的兴衰史,介绍了 iOS 11 在提高用户易用性的同时可能会破坏部分安全性: https://blog.elcomsoft.com/2017/11/ios-11-horror-story-the-rise-and-fall-of-ios-security/
-

[ IoTDevice ] Hacking 智能家居设备,来自 H2HC 2017: https://goo.gl/VeV9Nf
-

[ macOS ] Why <blank> Gets You Root,Objective-See 研究员对昨天爆出的 macOS ROOT 空密码提权 Bug 的分析: https://objective-see.com/blog/blog_0x24.html
-

[ Malware ] Android 恶意软件伪装成色情应用攻击中国用户: https://www.symantec.com/blogs/threat-intelligence/android-malware-porn-apps-chinese
-

[ Malware ] 银行木马通过伪造的韩国 CERT 安全通告进行传播: https://info.phishlabs.com/blog/banking-trojan-dropped-through-spoofed-korean-cert-bulletin
-

[ Others ] Understanding Ethereum Smart Contracts: http://www.gjermundbjaanes.com/understanding-ethereum-smart-contracts/
-

[ Others ] 图像隐写之使用PHP隐藏图像中的文本: http://thedebuggers.com/image-steganography-hiding-text-using-php/ , Demo : https://www.youtube.com/watch?v=qH0wLIwZa0U
-

[ Tools ] stacks-cli - 用于一键分析网站所用技术栈的命令行工具: https://github.com/WeiChiaChang/stacks-cli
-

[ Tools ] exploit-database-papers - Exploit Database's Papers: https://github.com/offensive-security/exploit-database-papers
-

[ Tools ] malsub - 用于在线恶意软件分析和威胁情报服务的 Python RESTful API 框架: https://github.com/diogo-fernan/malsub?utm_content=buffer51301&utm_medium=social&utm_source=twitter.com&utm_campaign=buffer
-

[ Vulnerability ] Qemu 的 NBD server 实现在接收客户端请求时,一个超长的 export name 会触发栈上的越界写漏洞(CVE-2017-15118): https://bugzilla.redhat.com/show_bug.cgi?id=1516922
-

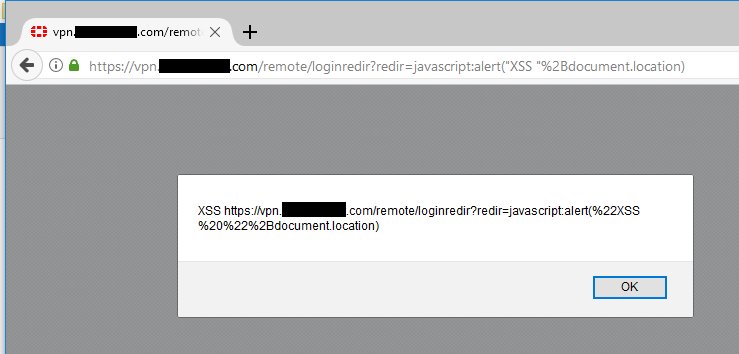
[ Vulnerability ] FortiGate SSL VPN Portal XSS 漏洞: https://www.sec-consult.com/en/blog/advisories/fortigate-ssl-vpn-portal-xss-vulnerability/index.html
-

[ Vulnerability ] UEFI BIOS holes:UEFI BIOS Rootkits 与 Intel Direct Connect Interface 漏洞的挖掘和利用: https://goo.gl/pV6wfV
-

[ Windows ] Win32k NtUserOpenDesktop->OpenDesktop 拒绝服务 PoC,影响 Windows 8 到 Windows 10 RS4(17046) 版本: https://gist.github.com/hfiref0x/6e726b352da7642fc5b84bf6ebce0007
-

[ Windows ] 利用 Windows 系统内置的域用户密钥缓存工具 cmdkey 辅助渗透提权: https://www.peew.pw/blog/2017/11/26/exploring-cmdkey-an-edge-case-for-privilege-escalation
-
-

[ Linux ] Huge Dirty COW - Incomplete Dirty COW, Bindecy 团队在对 Linux 内核 Dirty COW 漏洞(CVE-2016–5195)补丁分析后发现补丁后仍有问题(CVE-2017–1000405): https://medium.com/bindecy/huge-dirty-cow-cve-2017-1000405-110eca132de0 https://github.com/bindecy/HugeDirtyCowPOC
-

[ SecurityReport ] McAfee Lab 对 2018 年的威胁预测: https://securingtomorrow.mcafee.com/mcafee-labs/2018-threats-predictions/
-
-
-

[ Tools ] PartiSan: Fast and Flexible Sanitization via Run-time Partitioning(paper): https://arxiv.org/pdf/1711.08108.pdf
-

[ Virtualization ] 云计算环境 AWS EC2 虚拟化的发展历程: http://www.brendangregg.com/blog/2017-11-29/aws-ec2-virtualization-2017.html
-

[ Windows ] 如何在 Windows 10 系统启用基于虚拟化(Hyper-V)的系统保护特性(HVCI): https://docs.microsoft.com/en-us/windows/device-security/enable-virtualization-based-protection-of-code-integrity