腾讯玄武实验室安全动态推送
Tencent Xuanwu Lab Security Daily News
-

[ Backdoor ] 如何在 Windows PE 文件中植入一个无法检测到的后门: https://haiderm.com/fully-undetectable-backdooring-pe-files/
-

[ Firmware ] Intel 通过内部审计,最近修复了 Intel ME 11.x, SPS 4.0, TXE 3.0 的多个漏洞: https://security-center.intel.com/advisory.aspx?intelid=INTEL-SA-00086&languageid=en-fr
-

[ Industry News ] Cobalt 团伙再次来袭:利用宏和 CVE -2017-8759 制作恶意文档结合钓鱼手段攻击俄罗斯银行: http://blog.trendmicro.com/trendlabs-security-intelligence/cobalt-spam-runs-use-macros-cve-2017-8759-exploit/
-

[ Linux ] Linux 内核 net/ipv4/inet_connection_sock.c inet_csk_clone_lock Double Free 漏洞(CVE-2017-8890)PoC: https://github.com/hardenedlinux/offensive_poc/tree/master/CVE-2017-8890
-

[ Linux ] TSH - 一个开源的 Linux 后门: https://github.com/orangetw/tsh
-

[ MalwareAnalysis ] SunOrcal 恶意软件变种的分析报告: https://researchcenter.paloaltonetworks.com/2017/11/unit42-sunorcal-adds-github-steganography-repertoire-expands-vietnam-myanmar/
-

[ MalwareAnalysis ] McAfee 对一款可能与 Lazarus 网络犯罪集团有联系的 Android 恶意软件的分析: https://securingtomorrow.mcafee.com/mcafee-labs/android-malware-appears-linked-to-lazarus-cybercrime-group/
-

[ Others ] Hunting with Splunk: https://www.splunk.com/content/splunk-blogs/en/2017/07/06/hunting-with-splunk-the-basics.html
-

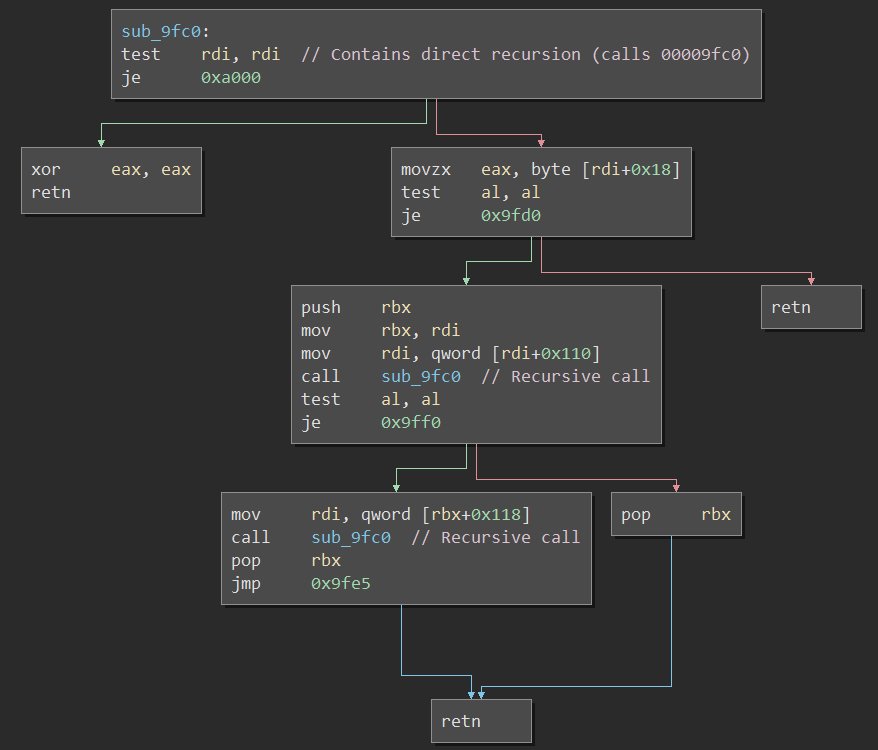
[ Others ] 使用递归攻击未初始化变量: https://signal11.io/index.php/2017/11/19/attacking-uninitialized-variables-with-recursion/
-

[ Others ] 基于抽象语法树(AST)的 PowerShell 代码混淆: https://cobbr.io/AbstractSyntaxTree-Based-PowerShell-Obfuscation.html
-

[ Others ] 使用 SCF 文件窃取用户 Hash: https://1337red.wordpress.com/using-a-scf-file-to-gather-hashes/
-

[ Pentest ] Meterpreter 渗透框架的 getsystem 命令是如何夺取 SYSTEM 权限的: https://blog.xpnsec.com/becoming-system/
-

[ Popular Software ] Embedi 团队公开了 Office EQNEDT32.EXE 内存破坏漏洞(CVE-2017-11882)的 PoC: https://github.com/embedi/CVE-2017-11882
-

[ Tools ] burp-molly-scanner - 将 BurpSuite 变成 Headless 的 Web 应用漏洞扫描器: https://github.com/yandex/burp-molly-scanner/
-

[ Tools ] Sn1per - 自动化渗透测试侦察扫描工具: https://github.com/1N3/Sn1per
-

[ Web Security ] 使用 XSS 窃取 CSRF Token: https://digi.ninja/blog/xss_steal_csrf_token.php
-

[ Windows ] Windows CiSetFileCache TOCTOU 漏洞,可以导致 Device Guard 安全特性的绕过(CVE-2017-11830): https://bugs.chromium.org/p/project-zero/issues/detail?id=1332
-

[ Windows ] 微软提供了一个 Windows 10 开发环境虚拟机,里面预装了 SDK、Visual Studio、Bash on Ubuntu on Windows 等等: https://developer.microsoft.com/en-us/windows/downloads/virtual-machines
-

[ Windows ] 利用 WMI 进行 C&C 通信: https://pentestlab.blog/2017/11/20/command-and-control-wmi/
-

[ Windows ] 如果系统级强制 ASLR 策略开启,那么 Windows 8+ 版本在处理应用级的地址随机化会出现问题: https://www.kb.cert.org/vuls/id/817544 https://twitter.com/i/web/status/932525090419478529
-

[ Windows ] Windows 下载远程 Payload 并执行任意代码的教程: https://arno0x0x.wordpress.com/2017/11/20/windows-oneliners-to-download-remote-payload-and-execute-arbitrary-code/
-

[ Windows ] 在 Windows 环境中追查凭证导出的痕迹,来自 2017 ZeroNights : https://www.slideshare.net/heirhabarov/hunting-for-credentials-dumping-in-windows-environment
-

[ Browser ] 如何比较不同浏览器的页面加载时间: https://hacks.mozilla.org/2017/11/comparing-browser-page-load-time-an-introduction-to-methodology/
-

[ Industry News ] Lazarus 犯罪团伙开始瞄准移动平台: https://securingtomorrow.mcafee.com/mcafee-labs/lazarus-cybercrime-group-moves-to-mobile/
-

[ Industry News ] OpenRASP v0.20 发布 | 性能提升与零规则漏洞检测: https://mp.weixin.qq.com/s/50AFAVp8dSwuc1ACY5kRKw
-

[ IoTDevice ] Finding RCE in HP’s Printer Fleet: https://foxglovesecurity.com/2017/11/20/a-sheep-in-wolfs-clothing-finding-rce-in-hps-printer-fleet/
-

[ Popular Software ] Running Openbts with the nuand bladerf on UBUNTU : https://blog.strcpy.info/2016/11/16/running-openbts-with-the-nuand-bladerf-on-ubuntu-the-definitive-guide/
-

[ Popular Software ] 深入分析Adobe Acrobat的类型混淆漏洞(CVE-2017-16379): https://cybellum.com/cy-2017-011-type-confusion-in-adobe-acrobat/ http://www.4hou.com/vulnerable/8504.html
-
-
-
-
-